At Google I/O 2014, it was a chance for Google to premiere the next version of Android for the smartphones and tablets; along with officially releasing Android Wear for wearables and Android variants for the car and the TV.
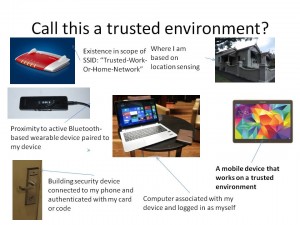
One feature that Google was promoting was the concept of a “trusted environment” for your Android smartphone where you don’t have to unlock the phone with your PIN or “pattern” routine to use it in that environment. Similarly, Apple just lately put forward a patent to implement this same “trusted-environment” concept in their iOS devices. Applications that were highlighted included you home, car or work and this was determined by one or more conditions being true.
For example, using a “voice unlock” routine can equate your voice as being a trusted user. Similarly, being connected to a particular Bluetooth watch or headset which is on and alive, or being in a particular location by virtue of association with a known Wi-Fi network segment or within range of a GPS “bearing” could also relate to a “trusted” environment. Apple’s implementation also is about about context-based behaviour such as bringing forward or disabling apps that relate to a particular environment, such as showing up a video-on-demand app when at home or disabling apps not safe for use when driving. It could extend to bringing forward a business-specific app like a “handheld electronic menu” for your favourite restaurant or an “online concierge” for your favourite hotel.
A good question is whether this concept of the “trusted environment” could be integrated with the Internet Of Everything? For example, the concept of having your mobile device near a computer or building-security device could be considered trusted as long as you authenticated with that device within a certain timeframe and/or with a particular key such as your own keycard or code.
This concept may not be considered appropriate in locations where there is a risk of your smartphones or similar device being stolen or accessed without your knowledge or permission. Examples of this may be a workplace where public and staff-only areas aren’t clearly delineated or a party or gathering that is happening at home. Personally, these setups also have to be about user privacy and about working totally to a user’s needs and habits.