Why do I defend Europe creating their own tech platforms?
Previous Coverage on HomeNetworking01.info ![Map of Europe By User:mjchael by using preliminary work of maix¿? [CC-BY-SA-2.5 (http://creativecommons.org/licenses/by-sa/2.5)], via Wikimedia Commons](https://homenetworking01.info/wp-content/uploads/2014/06/512px-Blank_map_europe_coloured.svg_-300x229.png)
Europeans could compete with Silicon Valley when offering online services
How about encouraging computer and video games development in Europe, Oceania and other areas
My Comments
Regularly I keep an eye out for information regarding efforts within Europe to increase their prowess when it comes to business and personal IT services. This is more so as Europe is having to face competition from the USA’s Silicon Valley and from China in these fields.
But what do Europeans stand for?
What Europeans hold dear to their heart when it comes to personal, business and public life are their values. These core values encompass freedom, privacy and diversity and have been build upon experience with their history, especially since the Great Depression.
They had had to deal with the Hitler, Mussolini and Stalin dictatorships especially with Hitler’s Nazis taking over parts of European nations like France and Austria; along with the Cold War era with Eastern Europe under communist dictatorships loyal to the Soviet Union. All these affected countries were run as police states with national security forces conduction mass surveillance of the populace at the behest of the dictators.
The EU’s European Parliament summed this up succinctly on their page with Europeans placing value on human dignity, human rights, freedom, democracy, equality and the rule of law. It is underscored in a pluralistic approach with respect for minority groups.
I also see this in the context of business through a desire to have access to a properly-functioning competitive market driven by publicly-available standards and specifications. It includes a strong deprecation of bribery, corruption and fraud within European business culture, whether this involves the public sector or not. This is compared to an “at-any-cost” approach valued by the USA and China when it comes to doing business.
As well, the European definition of a competitive market is the availability of goods or services for best value for money. This includes people who are on a very limited budget gaining access to these services in a useable manner that underscores the pluralistic European attitude.
How is this relevant to business and consumer IT?
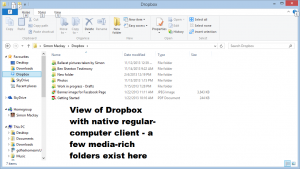
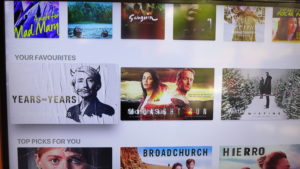
Nowadays, business and consumer IT is more “service-focused” through the use of online services whether totally free, complementary with the purchase of a device, paid for through advertising or paid for through regular subscription payments. Increasingly these services are being driven by the mass collection of data about the service’s customers or end-users with people describing the data as being the “new oil”.
Examples of this include Web search engines, content hosting providers like YouTube or SoundCloud, subscription content providers, online and mobile gaming services, and voice-driven assistants. It also includes business IT services like cloud-computing services and general hosting providers that facilitate these services.
Europeans see this very differently due to their heritage. Here, they want control over their data along with the ability to participate in a competitive market that works to proper social expectations. This is compared to business models operated by the USA and China that disrespect the “Old World’s” approach to personal and business values.
The European Union have defended these goals but primarily with the “stick” approach. It is typically through passing regulations like the GDPR data-protection regulations or taking legal action against US-based dominant players within this space.
But what needs to happen and what is happening?
What I often want to see happen is European companies build up credible alternatives to what businesses in China and the USA are offering. Here, the various hardware, software and services that Europe has to offer respects the European personal and business culture and values. They also need to offer this same technology to individuals, organisations and jurisdictions who believe in the European values of stable government that respects human rights including citizen privacy and the rule of law.
What is being done within Europe?
There are some European success stories like Spotify, the “go-to” online subscription service that is based in Sweden as well as a viable French competitor in the form of Deezer, along with SoundCloud which is an audio-streaming service based in Germany.
A few of the popular mobile “guilty-pleasure” games like Candy Crush Saga and Angry Birds were developed in Europe. Let’s not forget Ubisoft who are a significant French video games publisher who have set up studios around the world and are one of the most significant household names in video games. Think of game franchiese like Assassin’s Creed or Far Cry which are some of the big-time games that this developer had put out.
Then Qwant appeared as a European-based search engine that creates its own index and stores it within Europe. This is compared to some other European-based search engines which are really “metasearch engines” that concatenate data from multiple search engines including Google and Bing.
There have been a few Web-based email platforms like ProtonMail surfacing out of Switzerland that focus on security and privacy for the end-user. This is thanks to Switzerland’s strong respect for business and citizen privacy especially in the financial world.
There are some European voice assistants surfacing with BMW developing the Intelligent Personal Assistant for in-vehicle use while the highly-competitive telecommunications market in France yielded some voice assistants of French origin thanks to Orange and Free. Spain came in on the act with Movistar offering their own voice assistant. I see growth in this aspect of European IT thanks to the Amazon Voice Interopability Initiative which allows a single hardware device like a smart speaker to allow access to multiple voice-assistant
Technicolor, AVM and a few other European companies are creating home network hardware typically in the form of carrier-supplied home-network routers. It is although AVM are offering their Fritz lineup of of home-network hardware through the retail channel with one of these devices being the first home-network router to automatically update itself with the latest patches. In the case of Free.fr, their Freebox products are even heading to the same kind of user interface expected out of a recent Synology or QNAP NAS thanks to the continual effort to add more capabilities in these devices.
But Europe are putting the pedal to the metal when it comes to cloud computing, especially with the goal to assure European sovereignty over data handled this way. Qarnot, a French company, have engaged in the idea of computers that are part of a distributed-computing setup yielding their waste heat from data processing for keeping you warm or allowing you to have a warm shower at home. Now Germany is heading down the direction of a European-based public cloud for European data sovereignty.
There has been significant research conducted by various European institutions that have impacted our online lives. One example is Frauhofer Institute in Germany have contributed to the development of file-based digital audio in both the MP3 and AAC formats. Another group of examples represent efforts by various European public-service broadcasters to effectively bring about “smart radio” with “flagging” of traffic announcements, smart automatic station following, selection of broadcasters by genre or area and display of broadcast-content metadata through the ARI and RDS standards for FM radio and the evolution of DAB+ digital radio.
But what needs to happen and may will be happening is to establish and maintain Europe as a significantly-strong third force for consumer and business IT. As well, Europe needs to expose their technology and services towards people and organisations in other countries rather than focusing it towards the European, Middle Eastern and Northern African territories.
European technology companies would need to offer the potential worldwide customer base something that differentiates themselves from what American and Chinese vendors are offering. Here, they need to focus their products and services towards those customers who place importance on what European personal and business values are about.
What needs to be done at the national and EU level
Some countries like France and Germany implement campaigns that underscore products that are made within these countries. Here, they could take these “made in” campaigns further by promoting services that are built up in those countries and have most of their customers’ data within those countries. Similarly the European Union’s organs of power in Brussels could then create logos for use by IT hardware and software companies that are chartered in Europe and uphold European values.
At the moment Switzerland have taken a proactive step towards cultivating local software-development talent by running a “Best of Swiss Apps” contest. Here, it recognises Swiss app developers who have turned out excellent software for regular or mobile computing platforms. At the moment, this seems to focus on apps which primarily have Switzerland-specific appeal, typically front-ends to services offered by the Swiss public service or companies serving Swiss users.
Conclusion
One goal for Europe to achieve is a particular hardware, software or IT-services platform that can do what Airbus and Arianespace have done with aerospace. This is to raise some extraordinary products that place themselves on the world stage as a viable alternative to what the USA and China offer. As well, it puts the establishment on notice that they have to raise the bar for their products and services.