What is the “new computing environment” and how to go about it?
When I talk of laptops, wireless routers and network-capable printers, I make frequent references to a “new computing environment” that these devices can enable.
What is the “New Computing Environment”
 The “New Computing Environment” is a home computing environment that is based around portability and flexibility. The seed for this environment has been sown with the widely-publicised Intel Centrino campaign and is becoming stronger in a lot of households.
The “New Computing Environment” is a home computing environment that is based around portability and flexibility. The seed for this environment has been sown with the widely-publicised Intel Centrino campaign and is becoming stronger in a lot of households.
It consists of most of the computers in the house being laptop or notebook computers.It may also include the use of “all-in-one” desktop computers similar to the newer Apple iMacs or HP TouchSmart desktops. The goal is that these computers are able to be moved easily around the house at a whim.
This environment will also encompass the use of smartphones and tablet computers for secondary computing activities like casual Web browsing, email and use of social networks.
There is a Wi-Fi home network in place that is served by at least a wireless router that is the network’s Internet “edge”. The computers may connect to that router via Ethernet if they are close to it but are typically connected to that router using the Wi-Fi network segment.
What does this lead to
Increased flexibility
The key benefit is to increase flexibility when it comes to computer use. The major benefit is that you can relocate the computer as you need it. An example that was portrayed in an Intel Centrino radio ad that was played in the UK was someone who was writing out an email on a laptop being being interrupted by another household member who had come in to do the vacuuming. Then they are able to move somewhere quieter to do the rest of their work.
As well, the “New Computing Environment” also leads to increased “casual computing” setups like viewing sites like YouTube or Facebook while lounging around on the sofa; going through one’s email while relaxing in bed or flicking through online news sites while in the kitchen. I even wrote a short article on this site about the trend of young people visiting Websites while watching TV.
Catering to temporary workspaces
Another very common scenario is a household without a dedicated workspace. This is where the kitchen bench or the dining table becomes a temporary office. Some households may have a collapsible table like a card table or trestle table along with one or more folding chairs, set up in a lounge area or landing for use as a temporary workspace; or may have such furniture on hand to set up a temporary workspace as required. The “New Computing Environment” allows the user to shift the computer along with the rest of their work whenever they need to do something like set the table for a meal.
Even if a household has a dedicated workspace, there will always be the need to create another temporary workspace to suit another person’s work or study needs or to suit a different type of work.
Storage flexibility
Similarly, laptop computers are much easier to store when not in use. For example, they can be put in a drawer when not needed, as I have mentioned in an older article regarding use of a laptop as a kitchen PC. This allows the machine to be well out of harm’s way which can be of concern in a busy household or with some children and pets.
As well, the laptop is also more suited to households who have older “davenport” or “roll-top” desks which are capable of being closed up when not in use. Here, these computers can be used at and stored easily in these desks. It also allows these desks to become the elegant piece of furniture that they are known for.
Suitability with “downsized living”
This computing environment is becoming increasingly relevant with people who live in smaller houses and apartments; especially city apartments.
This class of user includes “empty-nest” parents who are moving to smaller premises because their children have left the family home, but still need to be able to look after their grandchildren when they come around. Here, their computing equipment doesn’t need to cause much space to be taken up in these smaller living quarters.
The “home-business” laptop
This kind of computing environment also suits the use of a “home-business” computer that is used at home but taken to the workplace while you are working. For some small-business operators, a large laptop like the Dell Inspiron 15R or the HP Probook 4520s may be the only computing device that they need to use for all their computing needs and you just pack this machine in the boot (trunk) of your car before you head to or from your workplace.
Implementation notes
Starting out
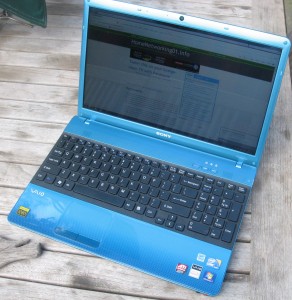
You will need to use a laptop computer that is commensurate to your computing needs. But it will have to be equipped with an integrated Wi-Fi wireless network interface of at least 802.11g WPA standard. This covers most laptops made over the past five years. I have reviewed plenty of laptops and notebooks on this site and will be reviewing more of them as they come along from different manufacturers. You can have a look at the list of equipment reviewed here on this page.
If you are intending to buy a new laptop computer, I would suggest that you look at the buyer’s guides that I have written – “Buying a Laptop or Notebook Computer”. Here, I have suggested the use of the 15” laptop computers as a sole or main computing device for this environment. If you have very basic needs like emailing and basic Web surfing, a unit equipped with a low-end processor and around 2Gb memory, like the Compaq Presario CQ42 that I have reviewed here, can suit your needs here. It is still worth it to spend as much as you can afford on the hard disk capacity because as you use the computer more regularly, you will end up filling the hard disk more quickly.
On the other hand, you may want to use an “all-in-one” desktop computer like one of the Apple iMac, HP TouchSmart Desktop or Sony VAIO J or L Series computers. These have the computing power, secondary storage and the screen integrated in one slim lightweight housing, with a separate keyboard and mouse. They may be useful as a “common” or “family” computer and can be stored or moved easily as long as you know how to reconnect the keyboard and mouse.
Printers
A lot of people who set up for the “new computing environment” typically use a direct-connected printer and bring the laptop closer to it in order to plug it in when they want to print or scan something.
What you need to do for proper implementation is to use a network-enabled printer. Here, these printers connect directly to the network either via Ethernet or Wi-Fi wireless and accept their print jobs through this connection. Multi-function printers can also expose their other functions like the scanner, fax or memory-card slots to the network.
This avoids the need to connect the laptop to the printer every time you want to print something out. With a network printer, you just select that printer from the list of printers when you specify a print job from your laptop and, moments later. you will find your print job in the printer’s output tray. Here, the job is sent via the network to the printer rather than via a cable that you always connect to the printer.
“Easing the gap” towards flexibility
Some users who are used to a regular laptop computer connected by Ethernet to a single-port broadband modem at a regular workspace may still get in to the habit of connecting the laptop to the wireless router using the “old way”. This is more so if they see their computer’s home location as being on the desktop near the router and while at that location they plug it in to the Ethernet socket on the router.
Some operating systems may react in a strange way if the user plugs in the Ethernet connection while the wireless connection is still active. This may be not of concern with newer operating systems that can automatically deactivate the Wi-Fi wireless network interface if the computer is connected to the network via an Ethernet cable. Here, the user needs to know how to manually enable and disable the Wi-Fi wireless network interface in the laptop.
Some of the computers will use a separate “Wi-Fi” button to turn the Wi-Fi modem on an off whereas more recent examples will require you to press the “Fn” key and a function key with a transmitter symbol to turn the wireless network on and off. This function may also be known as a “flight mode” and in some cases, will turn the Bluetooth function on and off at the same time.
Then what you might end up doing is to forget using the Ethernet cord and just use the laptop wirelessly as you realise you can use the Internet at home without wires.
Network-attached storage devices
If you are considering expanded or secondary data storage space for the “New Computing Environment”, you will be interested in buying a network-attached storage device. This is a dedicated external hard disk that is accessible from computers connected to your network. It is different to the idea of repurposing an old desktop computer as a shared storage server because the device is designed specifically to be a storage device and will end up being quieter, more efficient and more reliable to run than the old desktop computer.
They are relevant as a backup device; to offload rarely-touched data from your computer and/or to works as a standards-compliant media server for your music, digital pictures and videos. I have touched on this latter application in the DLNA Home Media Network series article: “Setting up for PC-free operation”.
An increasing number of wireless routers are offering NAS functionality when a USB hard disk is plugged in to them. This may be good for starting out or a temporary network-storage solution but a dedicated network-attached storage device can do the job much better for long-term use. As well, most of the routers that offer this function are very under-powered when it comes to handling USB hard disks and you would then have to use a self-powered USB hard disk or connect the “power” USB connection on small USB-powered hard disks to a powered USB hub.
Is wired technology relevant to the New Computing Environment
There are some cases where wired-networking technology is relevant to the New Computing Environment. One main case would be to support network printers or networked AV devices that don’t have integrated Wi-Fi functionality. This would be more so as you consider purchasing an Internet-enabled TV or Blu-ray player for your home and a lot of these devices may just have an Ethernet socket rather than Wi-Fi connectivity.
Another case would be to use a secondary access point to extend wireless-network coverage, such as with buildings that use thick walls made of brick, stone or similar materials; large buildings or outbuildings on a property.
Here, you may think that you have to lay Ethernet wiring through the premises and this may be expensive and of poor value if you aren’t renovating, extending or rewiring your building. In most cases, you could use HomePlug AV technology as your wired “no-new-wires” technology because this uses regular AC wiring as a data carrier.
Conclusion
What I am hoping to do with this is to explain the “New Computing Environment” that is becoming a major trend as far as home and small-business computing is concerned. This is where the computing environment is centred around the use of portable computers that connect to a wireless network.



