What is social sign-on?
A trend that is being associated with online services or applications is to provide “social sign-on” for new and existing users of these services. This is based around the concept of single sign-on where you use one set of credentials verified by one service to authenticate with one or more other services. This time, the credential pool that is used for authenticating users is your membership with a social network like Facebook or Twitter. The expression is sometimes extended to cover other authentication-data pools like Microsoft’s authentication services associated with Outlook.com/Hotmail, Windows 8 or XBox; or Google’s authentication services used for GMail and YouTube.
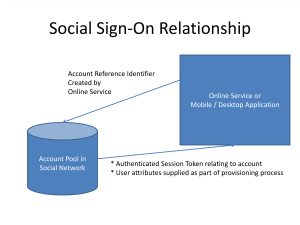
In a social sign-on arrangement, your credentials are held and tested at the social-network’s servers and both the online service and the social network create a unique “token” or “key” to link and authenticate your presence on these services. The common methods that these services use are based around the OAuth or OpenID protocols used for single sign-on across multiple services.
As well, your social attributes (name, birthdate, etc) that you have stored on the social network’s servers would be copied in to your account on the online service when this account is being provisioned. You will know about this when your social network pops up a screen asking you whether to allow the online service to gain access to your details held at the social network.
Advantages
There are some key advantages with using a social sign-on setup.
One is to benefit from a simplified provisioning process for your online service. This is without the need to key in the same data across multiple services. It also includes use of a pre-authenticated email address which is considered of high value with forums, commenting facilities and the like because most social networks especially Facebook, Google and Microsoft implement strong measures to combat fraudulent identities.
We also benefit because there are fewer sets of credentials to remember. As well, if a social network implements improved user-security measures like multifactor authentication or “trusted-device” operation, this flows on to the online service we use.
Some of the online services also can provide a personalised experience such as granting you birthday wishes on your birthday, including making those “special birthdays” such as the “big zeros” or the 21sts highly special.
Disadvantages
The disadvantages that can occur include weak links in the authentication protocols and a total dependence on access to and the security of a particular social-network account.
This also encompasses situations where a workplace or school may implement measures to shut out access to social networks in the name of productivity or an oppressive regime may shut out access to the popular social networks to curtail free speech. This can limit access to the online service because of its dependence on the social network.
How can it be operated properly
To assure users of their privacy, a social sign-on setup needs to identify any attributes that it is obtaining from a social network and give the user consent to obtain the attributes. As well, the login procedure should allow for one to create a login that is independent of a social network whether in conjunction with a social-network presence or not.
Similarly, the concept of social sign-on could be exploited by social networks and other authentication services to support simple-but-secure login for living-room applications. This is, from my experience, something that needs to be worked on because such devices require a lot of “pick-and-choose” data entry using a remote control’s D-pad to enter user credentials for online services. As well, many different users are likely to use the same living-room device.