A USB-C hub may take your Chromecast with Google Play further
Article

You can do more with your Chromecast with Google TV if you use a USB-C hub or dock that offers Power Delivery pass-through
Use a USB-C Hub to Upgrade Your Chromecast With Google TV (gizmodo.com)
My Comments
The Google Chromecast with Google TV device is actually an Android TV set-top box which has a lot of what Android can offer.
This includes being able to work with external peripherals thanks to device class support for some peripheral types that are connected via USB. It is thanks to Android TV having class drivers built in to the operating system in order to support these peripheral types.
What do I need?
USB-C hub must have Power Delivery pass-through connection
The USB-C hub or dock must have at least one USB-C port set up for Power-Delivery pass-through connectivity. This connection arrangement, which may be known as “Charge-through”, passes power from a USB-C PD charger to the host computing device that is connected to the upstream connection. This is in addition to providing power to the hub itself and any USB bus-powered peripherals connected to that hub.
USB PD-compliant charger with at least 45 watts power output
The USB charger that came with your Chromecast with Google Play device would not be able to power anything beyond the Chromecast device itself. This is because it is rated just for that device.
Rather you use a USB-PD compliant charger that offers at least 45 watts output and is something you would get with most of today’s ultraportable laptops that just use this connection. Using a USB-PD charger offering 65W or more may give you more flexibility especially if you are dealing with USB mass-storage devices or Webcams.
You may find that some if not most business-grade USB-C hubs and docks have their own power-supply arrangement and can provide power to the host computer in a USB Power-Delivery compliant manner. That is typically to provide power to an ultraportable laptop that is connected to these docks. These can be used without the need of a separate charger to connect to these hubs or docks – you just use the hub’s actual power supply and associated transformer to power your Chromecast setup.
What can I do?
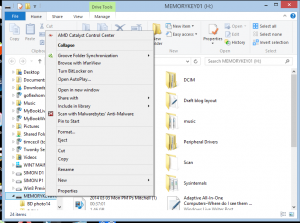
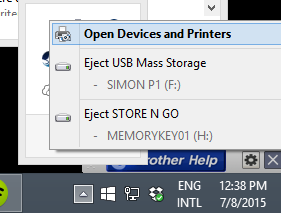
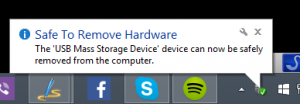
Play multimedia files held on USB mass-storage devices
If the USB hard drive, memory key or other mass-storage device (including memory cards in a memory-card reader) is formatted to FAT32, you may be able to view or play image, audio or video files held on that storage.
You may have to use a higher-powered USB PD charger if you are dealing with something like a portable hard disk or SSD. As for apps, software like VLC media player that can navigate the Android directory tree can work for finding content. There are also file managers available to the Android TV platform so you can see what is there on the storage devices.
A question that can be easily raised is whether this Android-TV-based Chromecast can support USB mass-storage devices that represent themselves as multiple volumes in one physical device. It is a situation that will come true with multi-slot memory-card readers, USB devices that have internal and external storage or USB storage devices partitioned in to multiple logical volumes.
Similarly, Android TV would need to support exFAT and the other open-source ext-based file systems in order to handle the high-capacity mass-storage devices as they should be handled.
Use of keyboards and mice as input devices
Connecting a USB keyboard or mouse, including a wireless one that uses a USB receiver dongle, provides an alternative input method for your Chromecast with Google TV.
For example, a keyboard can avoid the need to “hunt and peck” with your remote control when logging in to something like Netflix. This can also apply if you make heavy use of the search functionality within your favourite video-on-demand platforms. It can even apply if you are using an Android-TV-optimised Web browser to work the Web on the big screen.
This may even encourage Google to see Android TV as a viable TV-based gaming platform especially if they provide device-level support for wired or wireless games controllers be it USB Human Interface Device class controllers or device-specific support for XBox or PlayStation controllers. It also can lead to the creation of Android-TV-based hardware that has real gaming performance along with games that can take advantage of this performance.
To the same extent, Android TV support for USB-MIDI music devices could open up support for music-based applications and games on that platform. This could be ranging from music-based games through computer-based music training apps to music performance software.
Chromecast with Google TV as a group videophone
You can connect a Webcam to the USB-C hub so you can run this device as a group videophone. But you may find that some Webcams do need a bit more power and will need a stronger USB-PD charger on your setup.
As for software, Google’s Duo is the only videocall platform capable of supporting Android TV with the proper 10-foot “lean-back” user experience. You do need the app to be open and in the foreground when you are expecting a videocall on the Duo platform.
Google needs to encourage software developers who have videoconferencing software for the Android platform to write in Android TV support with the “lean-back” user experience. This could then have any TV or set-top device based on the Android TV / Google TV platform work well as a group videophone.
Infact Skype should reinstigate support for TV-based videocalling after they had many group videophone clients written for various smart-TV platforms.
More reliable Internet connectivity for your Chromecast
An increasing number of USB-C hubs are being equipped with Ethernet ports, primarily so that you can connect that ultraportable laptop to an Ethernet or HomePlug powerline network segment.
Let’s not forget that Google offered an Ethernet adaptor for their previous Chromecasts so these devices can be run from a more stable wired network segment. But they omitted an official Ethernet adaptor for the Chromecast with Google TV as part of its official aftermarket accessories lineup.
But the Ethernet connection on a USB-C hub is also available to the Google Chromecast with Google TV. It would be useful as a means to bring a reliable wired network connection to this device, especially if your home is wired for Ethernet, you have a HomePlug powerline network setup or your TV is next to your home network’s router.
Conclusion
Once you have USB-C hubs and docks that support common standard device classes for their internal connections or allow connection of peripherals honouring standard device classes, this could make Internet-of-Things and similar devices become very capable.
But these setups show a few glaring weaknesses within the Android TV ecosystem like lack of support for high-capacity file systems. It can be a chance for Google to take the Android TV platform further and turn it in to a highly-flexible large-screen set-top platform.