Some of the popular over-the-top messaging and VoIP platforms are being equipped for personal privacy and security.
This was a feature typically pitched at high-stakes business users but is now being pitched at everyday consumers thanks to the saga occurring in the USA between FBI and Apple where the FBI were wanting the encrypted data held on a suspect’s iPhone.
At the moment, WhatsApp and Viber are offering secure-communications features but this could be rolled out by other messaging/VoIP/videocall platform vendors like Skype, Facebook or Apple. For that matter, WhatsApp have recently made their platform from a subscription-funded platform to a free-to-user platform. They will continue to raise money by offering business-focused WhatsApp communications services.
Platform-wide best-case encryption by default
One of the main features is platform-wide end-to-end encryption which is implemented to “best-case standards” by default.
This means that the data that represents your calls and messages is encrypted by the end devices. Along with that, the user’s public and private keys associated with the encryption algorithm don’t stay on the company’s servers, thus not being at risk of a subpoena or other court order or government mandate. Rather, these are created by the end-user’s device and kept there.
The reference to “best-case” operation in this situation is that if the users are communicating with the latest version of the software that supports newer encryption algorithms, these algorithms are used for the encryption process. This even applies to group conversations where the “best-case” encryption method is implemented if all the correspondents are using the client apps that support that algorithm.
Authentication of contacts and their devices
As part of key exchange between contacts, there is an emphasis on authenticating one’s contacts with some systems like WhatsApp preferring a “face-to-face” method or others like Viber requiring you to read and confirm a password during a call. The former method that WhatsApp implements is for you to scan a QR code
Here, this is about whether you are really talking with the user on their device, in order to circumvent situations like lost or stolen phones, users installing their SIM cards in different devices and “man-in-the-middle” attacks. It was highlighted in Graham Cluley’s blog article about improving your security with WhatsApp.
This will typically be highlighted through the use of an indicator in your contact list that shows if a contact has been authenticated or if they have switched devices.
Concealed text/image conversations
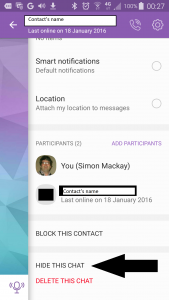
Viber introduced to their platform the ability for one to conceal a text/image conversation which can come in handy if you are exploiting their functionality to use tablets or regular computers as endpoints for Viber conversations.
Here, you can conceal the conversation so that others cannot see it unless they enter a user-set PIN or password. Situations where this can be necessary could include an innocuous activity like arranging that surprise event through a personal conversation held in a workplace to a traveller who leaves their iPad in their hotel room which can easily be visited by Housekeeping staff.
On the other hand, you could be able to specify whether a text/image chat is to be kept on each other’s devices or to disappear like what has been valued with Snapchat.
Features that could surface in the name of security
As other online-communications platforms jump on to the secure-communications bandwagon, there could be the rise of different features or variations on the above features.
For example, a communications-platform client could implement client-level user authentication where the software can be set up to require the user to log in to the client to start a conversation. Or the primary communications device like the smartphone has to be near a secondary communications client like a laptop before the user can run the software. This feature may be considered of importance with tablets and regular computers likely to be used by other users.
To some extent, an operating system that implements multiple-user operation could allow an online-communications client to switch user profiles and phone numbers so it works totally personally to the user.
There could be the ability for a user to mandate device-level authentication or encryption before a conversation takes place with a contact. This could allow for one to be sure they are talking to the right correspondent.
Other methods of verifying contacts and devices could surface such as the use of NFC “touch-and-go” or Bluetooth data exchange as a way of authenticating users’ devices. The software could also exploit other hardware or software “secure elements” like Trusted Platform Modules as an alternative to SIM cards for Wi-Fi-only tablets or regular computers.
This could even extend to such things as “trusted networks” or “trusted locations” where your caller can know that you are talking privately, based on factors like wireless-network parameters or proximity to particular Bluetooth devices.
Conclusion
What is now happening is that secure online conversations, once a feature that was enjoyed by big business and government, is now becoming available to every individual in the street for free. This allows them to have online conversations without being eavesdropped upon.