Article

The sale of a property is an area where consumers can easily be caught up in a business-email compromise scam
Email crooks swindle woman out of $150K from home sale | Naked Security blog
My Comments
Ordinary householders can be at risk of a “business email compromise“ phish attempt in the same way as those in large business.
The business email compromise scam
This scam typically has the trickster research as much as they can about their victim and his or her employer or business partners. The victim that is usually targeted is someone who is likely to facilitate business-sensitive transactions or handles business-sensitive data like the payroll. They will find out whom they report to within the organisation such as the chief financial officer, or beyond the organisation like their accountant, lawyer or the tax department.
Then they place an urgent request to the victim to wire funds to a particular account as part of a wire fraud. Or they could be asked to reply to the email with organisationally-sensitive data like employee data typically presented as a “wages and tax-witholding” statement like a W2 (USA), P60 (UK and Ireland) or Group Certificate (Australia) to facilitate identity theft against the business’s staff.
How can ordinary people get caught up in these scams?
But this kind of email scam can similarly happen with personal transactions, especially those that are high-stakes in nature, typically requiring the engagement of legal counsel. A key example of these transactions would be the sale of real-estate, businesses or investments.
Similarly, the probate settlement of a deceased estate or a property settlement after a divorce or separation could be at risk because these can involve a collection of items including high-value goods like real-estate or collectables. In that case, you are dealing with a real-estate transaction along with the valuation and sale of items.
It can also extend to transactions where you are delegating an agent to manage assets. Examples of these include trust funds typically for minor children, powers of attorney, or rental properties managed by a property manager or estate agent.
These transactions typically involve the frequent exchange of documents during the closure or settlement period where the transaction is in the process of being realised. They also involve dealing with different entities like conveyancers, law firms, estate agents and the like to facilitate the transactions. In addition, due to electronic transaction technologies like online document signing, there will be many emails between the parties that will have links to various resources like document repositories including document-signing platforms or results pages. They are also vulnerable towards the end of the settlement period where a last-minute change could be rushed in “under the radar”.
What can happen, for example, is that a fraudulent email could be used to “steer” the proceeds of a house sale away from the vendor’s account towards a fishy-sounding account. Or funds due to an estate’s beneficiary could be steered away to an account not under the control of that person.
What can you do?
To protect yourself, make sure everything about the transaction is properly “cut and dried” as it evolves. This includes identifying and documenting sources, currencies and destinations of any funds along with procedures affecting the high-stakes transaction at the start of the transaction. Especially be careful of last-minute changes that crop up towards the end of the settlement.
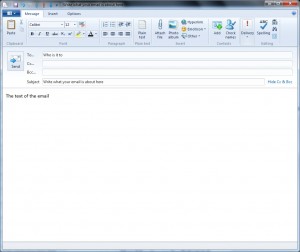
Protect email accounts that are party to the transaction such as implementing security measures that the email service or client software would provide. With Webmail services,using multi-factor authentication may work as a secure measure, as will verifying that you log in to the service at its known proper address.
Carefully examine emails associated with the transaction to be sure they come from the proper email addresses. As far as links to online resources are concerned, make sure you know the proper domain name for these resources and that the links point to resources at that domain name. Attachments should also come through as proper representations of their filetype and you may have to use your endpoint security software to scan for document-laden malware.
Similarly, you may have to make sure Word documents or Excel spreadsheets are viewed in “Protected View” where macros cannot be run or the document can’t be edited. You would need to exit this mode if you are editing the document such as filling in a form or amending a spreadsheet, or printing it out.
In some cases, a regular personal computer running desktop applications and Web browsers may become a better device to use for verification than a mobile-platform device like a smartphone or tablet. This is because the desktop operating system and software tends to offer a more detailed user experience than their mobile equivalents.
If someone changes their email or other communications details, confirm these details through another communications means that you and them trust. You may have to use one of the prior or alternate communications details as a tool for confirmation if a significant number of details is changed such as through a change of employment.
You may have to double-check invoices, account numbers and the like directly with the other party especially if these details are changed. It is best to do this in person or on the phone using independently-verified phone numbers such as numbers you already have for them.
Avoid the use of untrusted networks like insecure public-access networks to do your sensitive business. Here, you may find that using a mobile-broadband connection and/or a VPN may work with this kind of business if you are away from home or office networks you can trust.
Be especially careful about creditors where the payment-destination account number, the payment method or currency changes during the course of your business. There may be a legitimate reasons such as a creditor changing banks or accounts for something that suits their needs better. But an impostor could be steering money that you owe them to an account under the control of the grifter who is impersonnating them.
If the high-stakes transaction has any international dimension about it, don’t be afraid to seek consular help regarding any aspect of that transaction. It may mean talking with your country’s foreign-affairs government department or the embassy or consulate associated with the foreign country. This is now important with people relocating overseas while maintaining assets like homes in their own or other countries, or goods being purchased via the Internet from foreign sellers.
For example, participants of a transaction conducted across international borders can use consular help to verify each others’ identities. Similarly, they can organise official translation of any official documents that are part of the transaction and are in a language that one of the parties doesn’t understand. Or you simply may need to confirm the legitimacy of that transaction in the foreign country including any steps you need to take.
Conclusion
We as consumers can become vulnerable to the business-email compromise scam when we are dealing with high-stakes transactions like real-estate purchases. To protect yourself, it’s about secure computing and email practices along with making sure everything in the transaction is “cut and dried” including verifying changes through another communications path you trust.