Across-the-room data transfer–many questions need to be answered
The industry has explored various methods for achieving point-to-point across-the-room data transfer and user discovery. This would avoid the need to use the Internet or a mobile phone network to share a file or invite another user to a game or social network. Similarly, it would be a way to exchange data with a device like a printer or an interactive advertising setup in order to benefit from what that device offered.
Methods that have been tried
The first of these was IrDA infra-red transfer working in a similar to how most TV remote controls work to allow you to change channels without getting off the couch. This was exploited by the legendary Palm Pilot PDA and some of the Nokia mobile phones as a way to “beam” one’s contact details to a friend or colleague with the same device.
Bluetooth pushed forward with the Object Push Profile and File Transfer Profile as methods for exchanging data across the room. This was typically useful for contact details, low-resolution photos or Weblinks and was exploited with the popular feature phones offered by the major phone manufacturers through the 2000s. This method was also exploited by the out-of-home advertising industry as a way to convey Weblinks or contact details from a suitably-equipped poster to suitably-equipped mobile phones set to be discoverable.
But Apple nipped this concept in the bud when they brought out the highly-popular iPhone. The concept has been kept alive for the regular-computer operating systems and for Android mobile applications but mobile users who want to exchange data would have to ask whether the recipient had an Android phone or not.
Bluetooth also implemented that concept with the 4.0 Low Energy Profile standard by using “beacons” as a location tool. But this would be dependent on application-specific software being written for the client devices.
Microsoft is even reinstigating the Bluetooth method to transfer files between two computers in the same room as part of the functionality introduced in the Windows 10 April Update. But I am not sure if this will be a truly cross-platform solution for Bluetooth as was achieved with the earlier Object Push Profile or File Transfer Profile protocols.
Apple tried out a method similar to Bluetooth Object Push Profile called AirDrop but this implemented Wi-Fi-based technology and could only work with the Apple ecosystem. It was associated with “cyberflashing” where lewd pictures were forced out to unsuspecting recipients and Apple implemented a “contacts only” function with contacts’ emails verified against their Apple ID email logins as a countermeasure against this activity.
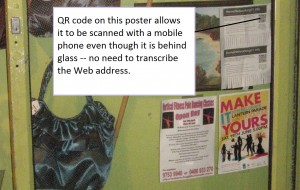
The QR code which is a special machine-readable 2D barcode has the ability to convey contact details, Weblinks, Wi-Fi network parameters and other similar data to mobile phones. These can be printed on hard-copy media or shown on a screen and have a strong appeal with business / visiting cards, out-of-home advertising or even as a means for authenticating client devices with WhatsApp.
Facebook even tried implementing QR codes as a way to share a link to one’s Profile or Page on that social network. Here, it can be a secure method rather than hunting via email or phone number which was raised as a concern with the recent Facebook / Cambridge Analytica data-security saga,
The Android and Windows communities looked towards NFC “touch-and-go” technology where you touch your phones together or touch an NFC card or tag to transfer data. This has been exploited as a technique to instigate Bluetooth device pairing and implemented as a method of sharing contact data between Android and / or Windows devices. For a file transfer such as with contact details, the data itself is transferred using Bluetooth in the case of Android Beam or Wi-Fi Direct in the case of Samsung’s S Beam feature.
The Wi-Fi Alliance are even wanting to put up a Wi-Fi-based method called Wi-Fi Aware. Here, this would be used for data transfer and other things associated with the old Bluetooth Object Posh Profile.
This is implemented on a short-range device-to-device basis because users in the same room may not be connected to the same Wi-Fi Direct or Wi-Fi infrastructure network as each other. There is also the reality that a properly-configured Wi-Fi public-access network wouldn’t permit users to discover other users through that network and the fact that a typical Wi-Fi network can cover the whole of a building or a street.
But there could be the ability to enable data transfer and user discovery using Wi-Fi Aware but being able to use a Wi-Fi infrastructure network but allow the user to define particular restrictions. For example, it could be about limiting the scope of discovery to a particular access point because most of these access points may just cover a particular room. Using the access points as a “scoping” tool even if the host devices don’t connect to that network could make the concept work without jeopardising the Wi-Fi infrastructure network’s data security.
Applications
There are a series of key applications that justify the concept of “across-the-room” data transfer. Typically they either involve the transfer of a file between devices or to even transfer a session-specific reference string that augments local or online activity.
The common application here is for a user to share their own or a friend’s contact details with someone else as a vCard contact-detail file. Another common application is to share a link to a Web-hosted resource as a URL. But some users also use across-the-room data transfer to share photos and video material such as family snapshots.
In the same context, it could be about a dedicated device sending or receiving a file to or from a regular computer or mobile device as outlined below for advertising. But it can also mean having a printer, NAS storage or smart TV being a destination for a file such as a photo.
In the advertising and public-relations context, “across-the-room” data transfer has been seen as a way to transfer a URL for a marketer’s Website or a visual asset to an end-user’s phone or computer. For example, the QR code printed on a poster has become the way to link a user to a media-rich landing page with further explanation about what is advertised. Similarly some out-of-home advertising campaigns implemented the Bluetooth Object Push Profile standard as a way to push an image, video or Weblink to end-users’ mobile phones.
But “across-the-room” data transfer is also being used as a way for users in the same space to discover each other on a social network or to identify potential opponents in a local or online multiplayer game. I find this as a preferred method for discovering someone to add to a social network or similar platform I am a member of so that I can be sure that I am finding the right person on that platform and they are sure about it. Also, in the case of a local multiplayer game, the players would have to continue exchanging data relating to their moves using the local data link for the duration of their game.
Facebook even explored the idea of using QR codes as a way to allow one to invite another person whom they are chatting with to be their Facebook Friend or discover their Facebook Page. It is infact an approach they are going to have to rediscover because they are closing off the users’ ability to search for people on the social network by phone number or email thanks to the Cambridge Analytica scandal.
What does the typical scenario involve?
The users who are in the same area are talking with each other about something that one of them has to offer such as contact details or a photo. Or, in the context of advertising or other similar situations, there will be some prior knowledge that there is something to benefit from knowing more about the offer using an online experience.
One of the users will invoke the transfer process by, for example, sharing the resource or hunting for a potential game opponent using their device’s user interface. The other use will share a nickname or other identifier to look out for in the list that the initial user is presented.
Then the other user will confirm and complete the process, including verifying success of that transfer and agreeing that the contents are what they were expecting. In the case of adding another user to a social network or multiplayer game, they will let the instigating user know that they have been added to that network or game.
What does a successful across-the-room data transfer or user-discovery ecosystem need?
Firstly, it needs to be cross-platform in that each device that is part of a data transfer or user/device discovery effort can discover each other and transfer data without needing to be on the same platform or operating system.
Secondly, the process of instigating or receiving a data transfer needs to be simple enough to allow reliable data transfer. Yet end-users’ data privacy should not be compromised – users shouldn’t need to receive unwanted content.
The protection against unwanted discovery or data transfer should be assured through the use of time-limited or intent-based discovery along with the ability for users to whitelist friends whom they want to receive data from or be discovered by in the wireless-based context. Intent-based discovery could be to have the recipient device become undiscoverable once the recipient device confirms that they have received the sender’s data or, in the case of a local multiplayer game, the players have completed or resigned from the game.
Conclusion
The concept of “across-the-room” data transfer and user/device discovery needs to be maintained as a viable part of mobile computing whether for work or pleasure. Where operated properly, this would continue to assure users of their privacy and data sovereignty.