Devolo Magic 2 Wi-Fi network extender kit that works on G.Hn HomeGrid powerline network technology
The International Telecommunication Union’s G.Hn HomeGrid standard is expected to become a significant new direction in “wired no-new-wires” network technology. Such technology makes use of wiring infrastructure that is in place within a premises for purposes such as providing AC mains power, providing a telephone service or connecting a TV to an outdoor TV antenna or cable / satellite TV setup.
This is for both the in-premises local-area network and for the Internet / WLAN “access” network that brings your Internet service to your home-network router.
This technology primarily works as an alternate powerline / AC-wire network technology to the established HomePlug family of powerline-network technologies. But it is also competing with MoCA for the TV coaxial-cable medium and the G.Hn HomeGrid Forum took over the HomePNA standard for phone-line-based on-premises networks.
Media types
Powerline
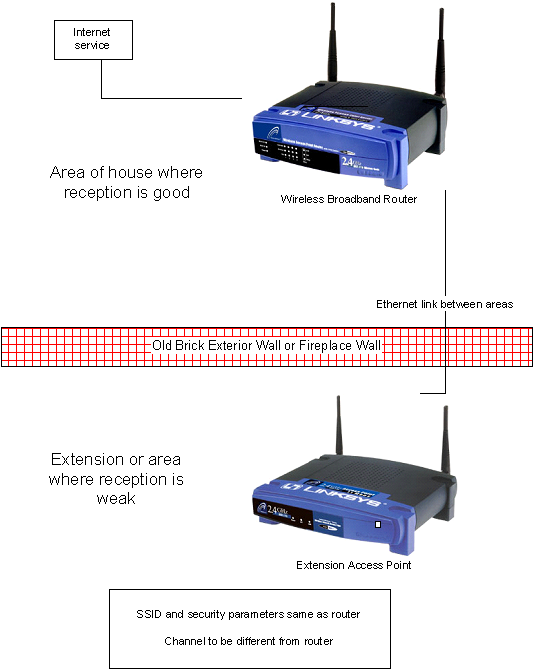
Use of a building’s AC wiring infrastructure is considered more credible due to the fact that there are many power outlets across a typical home. I have even had good experiences with this kind of network especially for extending Wi-Fi coverage or even extending a home network out to a detached garage that served as a “man-cave”.
The HomePlug Alliance had effectively abandoned continual development of the HomePlug series of powerline-network standards. At the moment, the latest standard is the HomePlug AV2 MIMO which can go to 2000Mbps, That is although a significant number of device manufacturers and IT retailers are continuing to make devices that work to the 1200Mbps bandwidth.
G.Hn HomeGrid has taken the powerline network further by offering the HomeGrid MIMO variant that cam move at least 2000Mbps of data. Like the HomePlug AV2 MIMO standards, this uses the active / phase / line, neutral and earth / ground wires of the mains-power plug to carry the data, thus assuring users of robust data transmission across a building’s general AC wiring infrastructure better.

G.Hn HomeGrid powerline technology could appeal to apartment blocks where multiple powerline-based “wired no new wires” networks could exist
The G.Hn HomeGrid powerline network standards have been refined also to increase data transmission robustness where there are many powerline networks operated together. This would be, perhaps, a situation that takes place within a large multiple-premises building like an apartment block, shopping centre or office block and would suit today’s urban-design expectations of mixed-use multi-premises developments. Some people would also hold this true for a dense neighbourhood of terrace / townhouse, semi-detached or similar homes.
A G.Hn HomeGrid powerline network can co-exist with a HomePlug AV2 powerline network in the same building but isn’t directly compatible with each other. This is similar to first-generation HomePlug powerline networks operating alongside second-generation HomePlug AV / AV2 powerline networks.
Personally I see G.Hn HomeGrid being used to “take the powerline network further” to higher bandwidths, increased robustness, further distances (500 metres compared to 400 metres for HomePlug AV2 MIMO) and other future needs.
At the moment, Devolo are investing in this technology with their Magic series of powerline network products including some Wi-Fi access points and offering some of these devices to consumers.
But some other network-equipment vendors who have retail-market presence are offering at least a powerline-Ethernet adaptor that works to G.Hn HomeGrid standards as part of their powerline-network product ranges. It is a way for them to put a foot in the door for higher-bandwidth powerline network segments.
TV coaxial cable
Another medium type that is supported by G.Hn HomeGrid is the TV coaxial-cable infrastructure. This would be associated with cable TV, an outdoor TV antenna (aerial) or a satellite dish and there may be extra TV coaxial-cable sockets installed around the house so you can have additional TV sets or use an easily-moveable TV in other rooms.
The Multimedia Over Coax Alliance have created a standard for using TV coaxial-cable infrastructure. But G.Hn HomeGrid have seen intention in using this same medium for the same purpose and could be working it to higher capacities or increased robustness.
Phone line
Yet another medium type that is supported by this same standard is traditional telephone cabling. This was worked on by HomePNA but the HomeGrid Alliance took over that concern and embodied it in to the G.Hn HomeGrid standard.
This infrastructure would have come about for established homes where there are multiple phone sockets installed through the house’s lifetime. This would be due to the installation of extension phones or to allow one to move a corded phone between different locations easily before cordless phones became a cost-effective approach to flexible landline telephony.
Use profiles
The G.Hn standards implement two relevant use profile cases.
One is called HomeGrid which describes connecting network devices within the premises as part of a local area network.
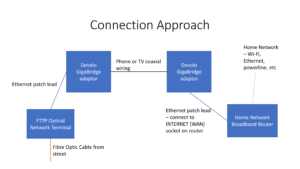
The other is called Gigawire and is described as being for “access” connectivity. This is to connect between the network’s router WAN (Internet) connection and a modem that is used for providing Internet service. This use case encompasses fibre-copper setups within extant multiple-premises buildings used to provide Internet to each premises with the building. Or it can encompass a single-premises building where the modem associated with the Internet service is installed in an inconvenient location but the Wi-Fi router has to be installed in the centre of the premises for best results.
All of the media connectivity types such as powerline, phone line or TV coaxial cable are able to work in these different use profiles. But there is a question about whether the same medium type could be used for access or in-home connectivity at the same time.
Media-type agnostic approach
The G.Hn HomeGrid standard is being underscored as a media-layer-level standard for the “wired no-new-wires” networks with the goal to make it easier to bridge between different media types.
This could be about the arrival of lower-level bridge devices that link between the different media types with these devices not needing higher-level processing to do so. Most likely such devices will have the bridge functionality but also have a Cat5 Ethernet connection of some sort.
Further evolution of this standard
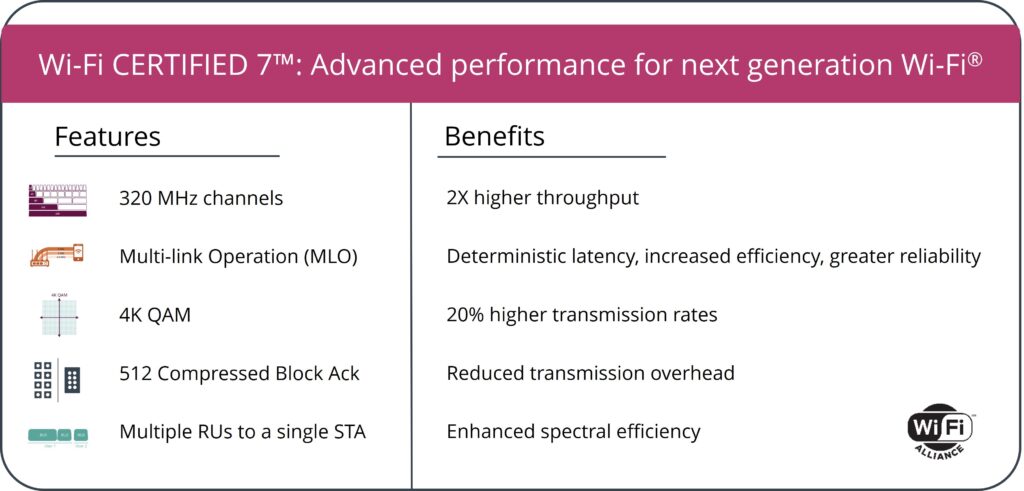
Currently this standard is being implemented as a “wired no-new-wires” approach to creating a multi-gigabit home network that has a bandwidth of 2.5Gbps or greater. It is to complement multi-Gigabit Ethernet and Wi-Fi 6/6E wireless network technology in raising your home network’s bandwidth making it fit for multi-gigabit broadband Internet services.
But there is further work needed to come about from G.Hn HomeGrid Forum for certain issues. For example, there will be a need to support VLAN network setups using the “wired no-new-wires” technologies. This would come in to play with routers that support a “guest network” or “community network” in addition to a primary network; or for VLANs that are used as a quality-of-service measure for VoIP or IPTV setups.
They would also have to examine the use of an access network and an in-premises network working on the same media bearer.
This could work with a fibre-optic extension setup that would normally use a G.Hn HomeGrid access network on a particular media type like phone line, power line or TV coaxial cable to bring the WAN (Internet) link from a garage or basement where the fibre-to-the-premises optical-network-terminal is installed to the living area where the home network router is installed. But the situation would change where that same basement or garage is purposed as a living space of some sort and a G.Hn HomeGrid in-premises LAN segment is to be created to make that space part of your home network.
Or there is the idea with a multiple-premises building where G.Hn HomeGrid technology is used for the in-building access network to each premises but there is a desire to extend a premise’s LAN or Wi-Fi to a common living area within the building.
Conclusion
The G.Hn HomeGrid and GigaWire standards are something that we have to watch and consider when it comes to “wired no-new-wires” network links for our home networks. In some cases, this technology may be about a “clean-slate” approach to your “wired no-new-wires” network segments.