Make sure you properly log off Web services when you are finished with a shared computer
A common situation that affects most home users is the existence of a desktop, laptop or tablet computer used by many people of the household. This computer may not just be used by members of the household but also by the household’s guests. I was infact talking about this with someone who had come in from overseas and was using a commonly-used iPad to work a few Web-based services like his GMail and Facebook accounts. Here, he and I were underscoring the need to properly log out of these services when done with them as well as clearing Web-browser history on these devices.
But as one operates their Web-based email, social-networking and other services using these computers, it can be easy to leave a session of these services going especially if you are called away for some reason. This could lead to other members of the household snooping around your account or doing something on that account in your name like playing a practical joke.
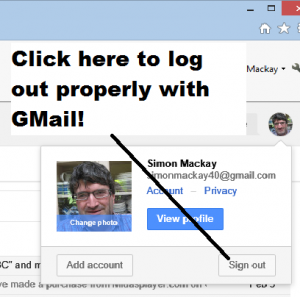
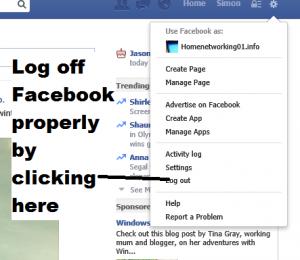
A wise practice with these computers is to make sure you log off your Web-based services as soon as you have finished with these services and before you leave the computer. To do this properly, you have to click or tap the “logout” or “sign out” button on the Web-based service’s user interface, which causes the service to log you out as far as it is concerned while cleaning up any cookies and other data held on your machine relating to that session.
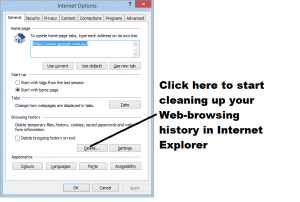
Similarly, clearing your Web browser’s history especially when finished using these commonly-used computers is also a wise practice. This avoids other users “tracking back” in to previous sessions for Web-based services or having people snoop on what previous users been browsing the Web for. The latter situation could either cause some nasty gossip to float around or, at worst, put the user in danger.
Use of multiple logins
Some operating systems like Windows and Android 4.2+ tablet implementations allow for the creation of separate accounts on that system so that each user can have their own operating environment. This can be beneficial because you can avoid the situation where someone can “snoop” around your Web history or someone’s Web email or social-network session that hasn’t been logged off properly.
Here, you could use one login as a “common-user” login while creating separate logins for the computer’s regular users. The regular users then use their own logins when they use the computer so they don’t have to worry about this kind of issue. Similarly, the separate logins can be personalised with wallpapers, “favourite Website lists”, customised colour schemes and the like as well as supporting application-level links to various social-network and other sites.
Windows 8 and 8.1 also implement a login setup which can be ported and synced across multiple computers thus allowing you to carry your computing environment between, say, a desktop and a laptop or to operate your computing environment on both your personally-used machine and a commonly-used machine.
Here, it is still a good practice to log off these accounts or enforce a lockout on them when you have finished at the computer so you can keep them private and less at risk of being meddled with.
Once you get in to the habit of logging off Web-service or user accounts on commonly-used computers and clearing Web history lists on these computers, you can avoid placing yourselves in a vulnerable position with your Internet use.