Article
Which Is More Vulnerable To Viruses And Hackers: Windows 10 or Mac OS X? | Gizmodo
My Comments
During the 2000s, the personal computing scene focused on so-called “regular” personal computers i.e. desktop and laptop computers that ran a desktop-grade operating system. The main platforms were the Windows platform heralded by Microsoft and with hardware made by plenty of other manufacturers and the Macintosh platform that was made by Apple. Of course, there were a few personal computers that ran one of many open-source Linux distributions which were effectively UNIX.
There was the issue of security risks magnified due to an increased amount of personal and business computing time spent online through the Internet. In most cases, especially with the Windows platform, these risks were mitigated using a desktop or endpoint security program installed on the client computer. Although I have constantly seen the Apple Macintosh platform at risk of security exploits, that platform wasn’t at risk because there were fewer computer users using that platform.
Enter Windows Vista. This operating system had improved security features like operating as a regular user unless necessary but these were tacked on to the Windows XP codebase. This led to poor performance and computer users saw the value of switching to the Apple Macintosh platform for regular computing needs with some even using Apple’s iWork office tools as a way simply to dump Microsoft.
This led to the Apple Macintosh platform becoming more vulnerable due to its increased popularity and the use of “write once run anywhere” code like Java. Apple had to pull their finger out to improve the Macintosh platform’s security and, like Microsoft, engage in regular software updates and patches.
Improvements
Major upgrades for pennies’ worth or free
Microsoft and Apple had even started to offer newer iterations of their operating systems to home users and small businesses at prices that would represent chump change or, later on, offer these iterations for free.
Apple started the ball rolling with Mac OS X for pennies’ worth starting with OS X Lion and for free starting with Mavericks. Subsequently Microsoft used Windows 8 to facilitate a software upgrade for pennies’ worth and used Windows 10 to instigate a free software upgrade program.
The major upgrades typically had security improvements like creation of app stores and newer secure codebases.
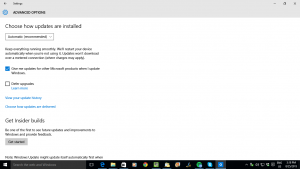
Blind updates for security patches
A way software developers keep their software going strong is to deliver updates and patches that rectify software bugs and allow the software to improve in performance. The delivery of these updates is being used to harden the software against known security exploits, often as soon as these holes are discovered.
This process typically involved users finding patches or newer code on the developer’s Website but Microsoft and Apple have put an end to this. Initially they set up a “one-stop-shop” program for downloading these updates including any peripheral-driver updates but have improved on this by providing for “blind updating”. This is where the operating system automatically downloads and installs these patches as soon as they become available.without you needing to do anything except, perhaps, reboot the computer when prompted.
Microsoft and Apple are even working on having these patches become effective once they are installed without you needing to reboot your computer. This is being achieved in the newer operating-system variants and with some newer patches.
The option for secure boot
Apple implemented in the Macintosh standard firmware a way to only let MacOS X boot on their Macintosh computers and this provided a sense of security because it can only allow these computers to run Apple-authorised code.
Microsoft and Intel are now implementing this through UEFI and Secure Boot which allows for authorisation of operating systems and pre-boot software that runs on a computing device. This has been considered controversial because it would wrest control of the computer from uses who may want to deploy Linux, especially a custom Linux distribution or wish to run with a dual-boot setup.
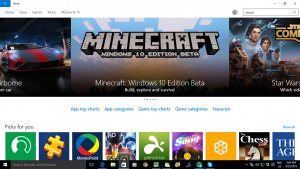
App stores and walled gardens
Another weapon that Microsoft and Apple are deploying comes from the world of mobile computing where mobile operating systems implement an “app store” which is a one-stop software “shopping mall”.
Like a suburban shopping mall with its physical goods, these app stores have tight controls on who can sell their software there. Here, the software has to be provided by an identifiable developer and approved and audited by the operating system developer who runs that app store.
There is also a requirement for the software to be sandboxed and have access to certain parts of the operating system rather than having full run of your computer.
Another factor that is also considered important is that if an application “does the right thing” by its users and the operating-system vendor, it is typically highly recommended or featured such as being given an “editor’s choice” or put in the “spotlight”. This gives the program increased exposure which attracts more installations and more purchases. As well, there are user-review mechanisms where people can uprate or downrate the software.
But both the Macintosh and Windows platforms require the ability to work with established software deployments that are typically installed via removable media or a download from the developer’s site. This is due to their legacy where people installed software from floppy disks or CDs or downloaded software from bulletin boards and download sites.
Windows 10 is providing a way to harden things further when it comes to this software in the form of Device Guard. This is a form of sandboxing which allows only certain programs to run on a computer but is made available to the Enterprise Edition only. It is because the process for setting up this whitelist would be considered very difficult for householders, small businesses and community organisations.
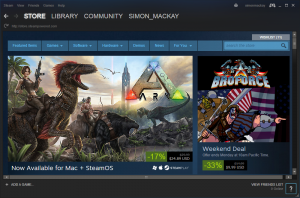
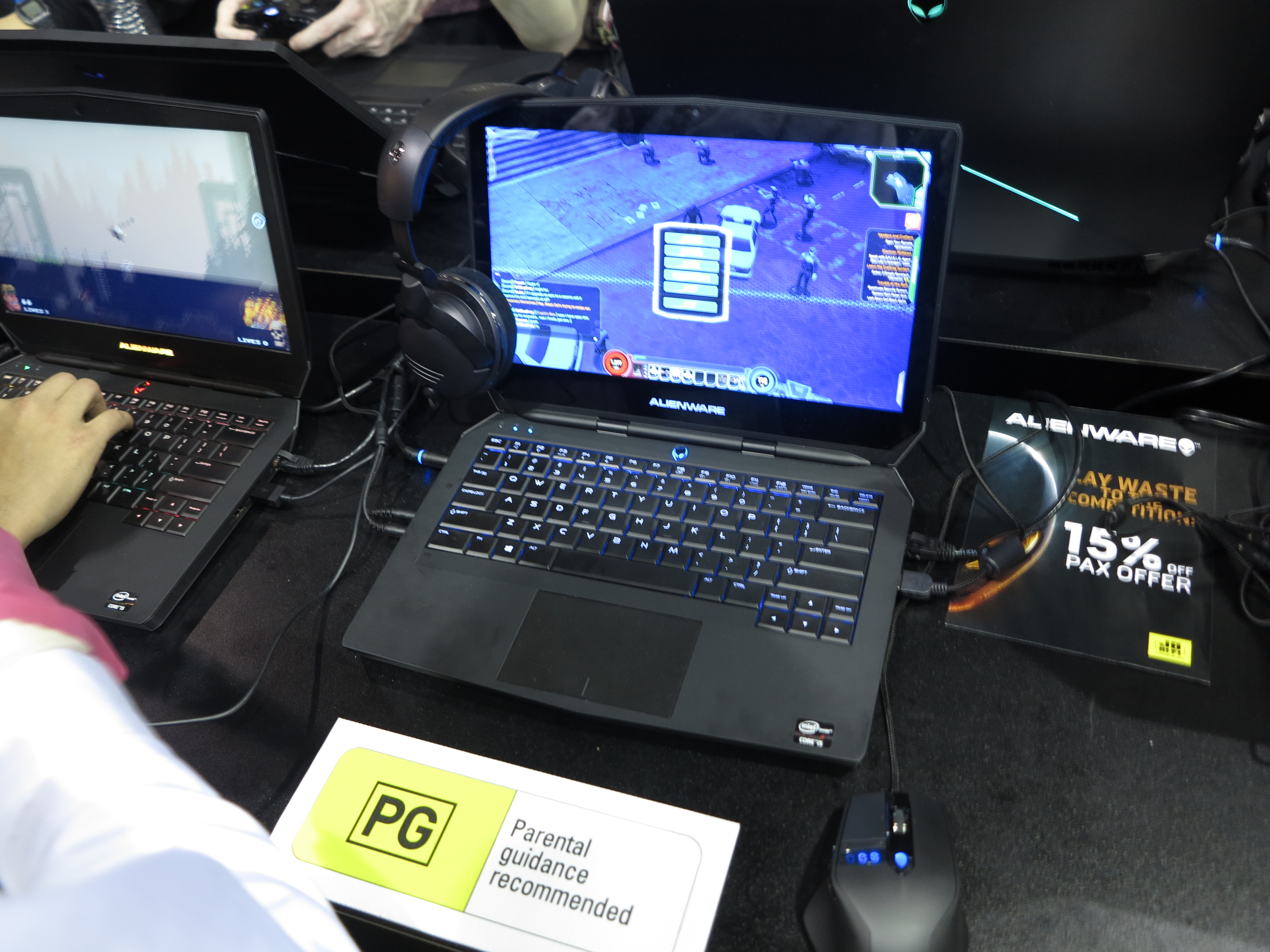
For games, major games studios are implementing their own app stores and games delivery systems in order to allow for cross-platform game and supporting-content delivery. Here, they want regular-computing gaming to have that same level of confidence associated with console or mobile gaming. This is although Apple and Microsoft deliver games through their app stores. The best example of this is Valve’s Steam online games shop but there are others like EA’s Origin.
Conclusion
What is happening is that for both the Windows and Macintosh computing platforms, they are being made more secure and malware-resistant and it is becoming a race between Apple and Microsoft to keep the regular computing environment as safe as a mobile computing environment.