What is remote-access and VPNs
The concept of remote-access and VPNs is primarily about gaining access to computer resources located in a location that is physically distant from where we are. The typical applications that we talk of are access to business data held out our small business’s shopfront from our home office’s computer or gaining access to data as we travel.
The method that is usually implemented is to set up a Virtual Private Network or VPN which is a virtual secure network link between one or more computers in one network and computers in another network. This link is hosted over another network infrastructure like an Internet service and acts as the secure data “tunnel” or path between these networks.
This will typically allow one to “draw down” files held on a remote hard disk or more likely use a “remote desktop” program to operate a computer from afar. The latter application would typically be performed using programs like VNC or Microsoft’s Remote Desktop / Terminal Services with a server component running on the host computer (which has the data and programs) and a remote-terminal client program on the computer that the user is working from.

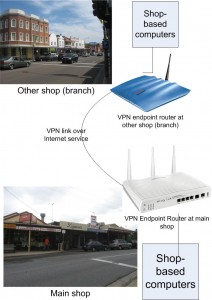
One of Draytek's VPN-endpoint ADSL modem routers
Previously, a VPN was based around two Internet-connected computers with one, typically a file server, being a “VPN server” and the remote computer being something like a laptop or home computer. Now the VPN can have a specially-enabled router as the “VPN server” or can become a secure link between two physical networks separated by an Internet connection and facilitated by specially-enabled routers.
Two types of VPN
There are two types of VPN setup that are in use. They are the “Client to Box” setup and the “Box to Box” setup.
“Client-to-Box” – Remote computer to local network
The “Client to Box” setup has a user operating a single computer to gain access to the remote network. This is typically used to allow a mobile worker or a telecommuter to gain access to company resources from their laptop or home computer.
The computer runs a “VPN-client” program that is either part of the operating system or a separately-supplied program. Here, this program provides the login experience for the user and authenticates the computer to the main network. Then it effectively “bridges” the computer’s resources to that network.

Single-Client Remote Access VPN
“Box-to-Box” – Connecting multiple logical networks
The “Box to Box” setup is simply a secure link that is established between networks established in different locations. The typical reason to do this is to avoid the costs of renting a dedicated line between the locations and use the economies of scale that the Internet offers. This is typically established with the use of special “VPN endpoint” routers joining the networks and these routers create a secure encrypted “tunnel” for the data to move between the networks.
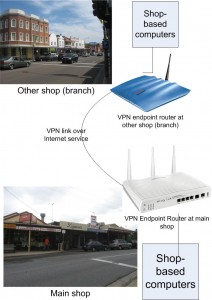
"Box-to-Box" VPN connecting two networks
Relevance to the small business and home users
These VPNs do appeal to small businesses and home users in many ways. One is to allow a shopkeeper to have access to data held at either their home office or their shop from the other location. Similarly, a small-business owner can establish a branch of their business in a new location and make sure they have access to the business resources at the main location from the branch’s network.
Another example for a “client-to-box” setup is to allow a tradesman or similar worker to gain access to customer data held on his home-office computer from the road through the use of a laptop computer connected by a wireless-broadband link or use of a wireless hotspot.
There is even the prospect of home users using this VPN technology to gain access to media held on a home media server from remote locations. One example would be to “pull up” audio material held on the home media server from one’s car using a wireless-broadband link to download or stream the material. Another example would be to have the same media that you have “at home” available on a home network installed at a secondary home that you own or rent.
As well, it could be feasible to use VPN technology as part of home security and automation, especially when it comes to managing remote properties.
Similarly, there can be the ability to support the use of the home network’s facilities in households where one or more members maintain separate Internet services and networks. Examples of this may include a business that is operated from home and a separate Internet connection for business-owned equipment; lodgers, students who want to have their own Internet use on their own terms
Limitations with the current technology
Hard to provision
The main limitation for home and small-business users when dealing with the VPN is that the VPN is typically hard to provision, whether it is to set up for the first time or to adapt it to suit future needs.
The user need to make sure each location’s local network uses a different IP address range which would be a difficult task especially as most small networks are set up to the IP-address specifications that are determined by default when you get the network-Internet “edge” router.
Then they need to know the VPN protocols, security protocols and the VPN passphrase and set these in the “hub” VPN endpoint. They have to make sure this is accurately copied and copy these details to the “spoke” VPN endpoints at the remote locations. Here they may become confused with determining which is “outbound” and which is “inbound” for each tunnel when configuring each endpoint.
They would also have to make sure that one of the VPN endpoints or the one that is to be the “hub” endpoint either has a fixed Internet IP address or can support a dynamic DNS service like DynDNS.org or TZO and is set up for this service.
Most of these tasks would then daunt most home and small-business computer users unless they had a lot of detailed computer knowledge and skills.
Limited protocol and application set
Most VPNs can only handle the protocols associated with bulk file transfer between two or more general-purpose printers. They don’t properly support device discovery for other devices which is important for the home and small-business user.
As well, they don’t work properly when it comes to streaming of real-time media between sites due to issues with streaming protocols and quality of service. Here, VPN applications involving these applications may have to implement application-layer gateways to facilitate the QoS and protocol needs.
Action to facilitate these networks
The UPnP Forum have released the “RemoteAccess” Device Control Profile for facilitation remote access and VPN use especially when it comes to supporting UPnP-compliant devices on the “other side” of a remote access link or VPN tunnel from “your side”. The first version is pitched at the “client-to-box” VPN setup, mainly to allow smartphone and laptop users to gain access to media on the home network. The second version, to be coming over the next year, is intended to support “box-to-box” setups like multi-site “super-networks”.
This has been released in conjunction with the “ContentSync” Device Control Profile which allows for synchronising of content collections (or parts thereof) between two UPnP AV MediaServer devices.
It has then made a relevant case for home users to value VPN and remote-access technology for personal-media applications such as keeping copies or subsets of media libraries at other locations or playing media held at one location from another location.
What needs to happen
Improve provisioning experience
The routine associated with provisioning a remote-access setup or VPN “super-network” needs to be simplified in a manner similar to what has happened to Wi-Fi wireless networking. Here, this was facilitated by the user not needing to work out any new data except to identify a wireless-network segment via its SSID.
In a VPN or remote-access network, the user sets up a “hub” endpoint which would work on machine-determined VPN protocol settings. Here, the user determines the location name, dynamic-DNS service or fixed IP address; and the VPN network password.
As well, a dynamic-DNS service that has a lot more “meat” such as increased reliability could be a service that is sold by carriers and Internet service providers as a value-added service. These services could typically be packaged as a product differentiator between different Internet-access-package lineups or just simply as an add-on item.
Then the user sets up a “spoke” endpoint or client terminal by providing the fully-qualified location name and the VPN network password as well as an identifier for the “spoke” endpoint.
This setup could support the use of machine-generated passwords that have been successfully implemented with Windows Connect Now easy-Wi-Fi setup method in Windows XP Service Pack 2 and Vista; as well as the HomeGroup password in Windows 7. Similarly, there could be support for configuration files like what has happened with Windows Connect Now – USB setup where a configuration file is uploaded to a Wi-Fi router or client device to facilitate quick wireless-network enrolment.
A client-to-box setup could be set up with the user entering the VPN name and password in to a VPN client program that is part of the computer’s or smartphone’s operating system.
Site-local subnets (logical networks)
The provisioning process for a “box-to-box” remote-access network should make it easy to create site-local subnets that are peculiar to each logical network. This could require the “hub” endpoint to keep track of the subnets and cause “spoke” endpoints to determine new subnets as part of the setup process.
It can include the ability to reinforce a DHCP “refresh” so that all network devices that are in a logical network obtain new IP addresses if the addressing scheme has to be redefined for that network. This is because most network devices in home and small business networks are allocated IP addresses using DHCP rather than the user defining them in order to simplify setup of equipment on these networks.
Use of a logo for easy-setup VPN systems
A VPN or remote access system needs to work to an industry standard that is supported by many vendors. Here, equipment and software that complies to this standard needs to be identified with a trademark and logo which denotes this compatibility so customers can choose the right hardware and software for an easy-to-provision remote access setup.
Retroactive upgrading programs
There are small businesses who run VPN setups that are typically based on VPN-endpoint routers that have existed for a long time and are currently in service. The standards for providing “easy-setup” VPN systems could be retroactively implemented in these units by applying updated firmware that incorporates this functionality to existing VPN-endpoint routers. This may happen more easily for devices that are based on open-source firmware.
Conclusion
Once the industry makes it easier for home and small-business users to establish or manage their remote-access setups and VPN-based multi-premises super-networks, the kind of features that larger businesses take for granted can be of benefit to this class of user.