Different kinds of cloud IT systems–what to be aware of
Very often “cloud” is used as a Silicon-Valley-based buzzword when describing information-technology systems that have any sort of online data-handling abilities.
This is more so if the IT system is sold to the customer “as a service” where the customer pays a subscription to maintain use of the system. It also is used where the user’s data is stored at an online service with minimal data-processing and storage abilities at the user’s premises.
It is because small business users are being sold on these systems typically due to reduced capital expenditure or reduced involvement in maintaining the necessary software. It also allows the small business to be able to “think big” when it comes to their IT systems without paying a prince’s ransom.
What is strictly a cloud system
But, strictly speaking, a cloud-based system relies on multiple online locations to store and/or process data. Such a system would have multiple computers at multiple data centres processing or storing the data, whether in one geopolitical jurisdiction or many depending on the service contract.
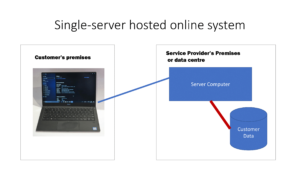
This is compared to the single-server online IT system sold as a service that implements at least a Web-based “thin-client” where you work the data through a Web page and, perhaps, a mobile-platform native app to work your data on a smartphone or tablet. Typically, the data would be held on one system under the control of the service provider with this system existing at a data centre. It works in a similar vein to common Internet services like email or Web-hosting with the data held on a server provided by the Wehhost or ISP.
Hybrid cloud systems
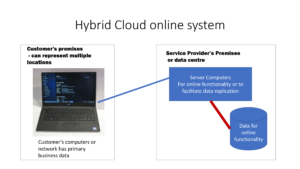
One type of cloud system is what could be best described as a “hybrid” system that works with data stored primarily on the user’s premises. This is typically to provide either a small private data cloud that replicates data across branches of a small business or to provide online and mobile functionality such as to allow you to manage the data on a Web page or native mobile-platform app anywhere around the world, or to provide messaging abilities through a mobile-messaging platform.
For example, a lot of NAS units are marketed as “cloud” NAS units but these devices keep the user’s data on their own storage media. Here, they use the “cloud” functionality to improve discovery of that device from the Internet when the user enables remote access functionality or data-syncing between two NAS devices via the Internet. It is due to the reality that most residential and some small-business Internet connections use outside IP addresses that change frequently.

WD MyCloud EX4100 NAS – one of the kind of NAS units that uses cloud functionality for online access
Or a small medical practice who keeps their data on-premises is sold a “cloud-based” messaging and self-service appointment-management add-on to their IT system. Here, the core data is based on what is held on-premises but the messaging functionality or Web-based user interface and necessary “hooks” enabling the mobile-platform native app for the self-service booking function are hosted on a cloud service built up by the add-on’s vendor. When a patient uses the mobile-platform app or Web-front to book or change an appointment, they alter the data on the on-premises system through the cloud-hosted service.
It may also be used with something like an on-premises accounting system to give business functionality like point-of-sale abilities to a mobile-platform device like an iPad through the use of a cloud-based framework. But the core data in the on-premises system is altered by the cloud-based mobile-platform setup as each transaction is completed.
Full-cloud systems
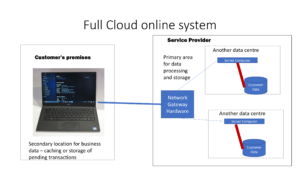
On the other hand, a full-cloud system has the user’s primary data held online across one or more server computers with minimum local hardware or software to work the user’s data. There may be some on-premises data-caching to support offline operation such as to provide transaction-capture if the link is down or simply to improve the system’s performance.
The on-premises data-caching can be extended to a system that has concurrent data storage both in the cloud and on the premises. This may help businesses who have invested in on-premises data-storage by providing them with the security and flexibility of a cloud setup with the fail-safe and responsive operation of the on-premises setup. In some cases, it may also be about facilitating secure payment-card transaction processing with that taking place in a separate compliant network hosted by the IT solution provider.
The IT infrastructure for a full-cloud system will have some measure of scalability to allow for an increasing customer base, typically with the service provider annexing more computer power as the customer base increases. Such a service will have tiered pricing where you pay more for increased capacity.
Client software types
The user-interface for an online or cloud IT system would primarily be Web-driven where you work the data with a Web browser. On the other hand, it could use native client software that works tightly with the client computer’s operating system whether as a “thick” client with a significant amount of local data-processing or storage on the endpoint computing device or a “thin” client which just has a window to the data such as simply using a Web browser.
Public vs private cloud
Another concept regarding cloud-based IT is the difference between a public cloud and a private cloud. The public cloud has the computing power managed by another firm like Microsoft Azure or Amazon Web Services while the private cloud has all its computing power managed by the service provider or client company and effectively isolated from public access through a separate private network.
This can be a regular server-grade computer installed at each of the business’s branches, described as an internal cloud, Or it can be multiple high-grade server computers installed at data centres managed by someone else but available exclusively for the business, known as a hosted private cloud.
Data Privacy, Security and Sovereignty
Another factor that comes in to question regarding cloud and online computing is the issue of data privacy, security and sovereignty.
This covers how the data is handled to assure privacy relating to end-users whom the data is about; and assurance of security over data confidential to the IT system’s customer and its end-users. It will call out issues like encryption of data “in transit” (while moved between systems) and “at rest” (while stored on the systems) along with policies and procedures regarding who has access to the data when and for what reason.
It is becoming a key issue with online services thanks to the European GDPR directive and similar laws being passed in other jurisdictions which are about protecting end-users’ privacy in a data-driven world.
The issue of data sovereignty includes who has effective legal control over the data created and managed by the end-user of the online service along with which geopolitical area’s rules the data is subject to. Some users pay attention to this thanks to countries like the continental-European countries who value end-user privacy and similar goals heavily.
There is also the issue of what happens to this data if the user wants to move to a service that suits their needs better or if the online service collapses or is taken over by another business.
Cloudlets, Fog Computing and Edge Computing
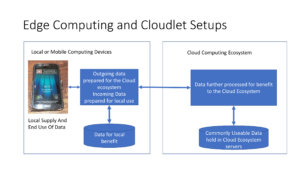
This leads me to the concept of “edge computing”, which uses terminology like “fog computing” or “cloudlets”. This involves computing devices relatively local to the data-creation or data-consumption endpoints that store or process data for the benefit of these endpoints.
An example can be about a small desktop NAS, especially a high-end unit, on a business premises that handles data coming in to or going out to a cloud-based online service from endpoint devices installed on that premises. Or it could be a server installed in the equipment rack at a telephone exchange that works as part of a content-delivery system for customers who live in the neighbourhood served by that exchange.
Similarly, the Qarnot approach which uses servers that put their waste heat towards heating rooms or creating domestic hot water implements the principle of edge computing. Even the idea of a sensor drone or intelligent videosurveillance camera that processes the data it collects before it is uploaded to a cloud-based system is also about edge computing.
It is being touted due to the concept of decentralised data processing as a way to overcome throughput latency associated with the public Internet links. As well, this concept is being underscored with the Internet of Things as a way to quickly handle data created by sensors and turn it in to a form able to be used anywhere.
Conclusion
Here, the issue is for those of us who buy service-based IT whether for our own needs or for a workplace is to know what kind of system we are dealing with. This includes whether the data is to exist in multiple locations, at the premises or at one location.
Originally published in July 2019. Updated in January 2020 in order to encompass cloud-based IT solutions that keep business data both in the cloud and on the premises as well as using cloud-based technology to facilitate secure transaction processing.