Multiple email accounts may be beneficial to your privacy and work-life balance.
Some of us may find it convenient to handle all of our email through one account. The advantages that are often seen include dealing with one inbox and sending from one account.
But we are increasingly entering a world where we have to deal with multiple email accounts.
Why run multiple email accounts?
One reason this is becoming important is to keep business and private email separate. Here, it may be about preserving a separate business and social persona, or simply to delineate your time between home and work activity. Similarly, the separate email address for business / work email is an advantage in preserving a professional appearance.
As well, the correspondence associated with your personal email address that you maintain yourself isn’t subject to the same kind of legal scrutiny that the correspondence associated with your business email address would be subject to. This is important if your workplace or business is to change hands or is a party to legal action of any sort.
 People who have a public-facing business life such as politicians or celebrities will maintain a public-facing email address to maintain an email correspondence consistent with that public-facing role. This is becoming more important where people in the public eye are becoming more vulnerable to “dirt-digging” – the practice of trawling for any information to discredit one’s reputation.
People who have a public-facing business life such as politicians or celebrities will maintain a public-facing email address to maintain an email correspondence consistent with that public-facing role. This is becoming more important where people in the public eye are becoming more vulnerable to “dirt-digging” – the practice of trawling for any information to discredit one’s reputation.
This practice is also becoming important with the emails we “tie” with various social-network presences. Here, we may want to operate a professional-looking persona on the public-facing social-media profiles while keeping a private persona that you have on your personal social-media profiles.
The situation extends to where we have our email address on material that the public have easy access to, whether it’s that notice on the church noticeboard or our entry on that petition.
Those of us who engage in online dating are having to find that maintaining a separate email address for use with dating apps and Websites gives us greater control over what potential suitors know about us. It may also offer a chance to control when they can contact us while keeping this life private from family or work.
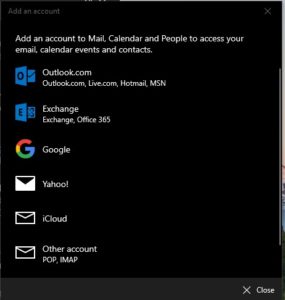
Account types list in the Add Account option including option to add POP3 or IMAP4 accounts
It also applies to businesses and organisations who maintain a public-facing email address that is written on the public-facing material. This keeps a professional appearance and keeps your staff’s business and private email more private. Similarly, you can maintain multiple email address for particular job descriptions or workflow requirements.
Conversely, some of us maintain a separate email address that we give to marketers or online email newsletters as a crude method of spam control. Similarly, separate email addresses are being seen as important as a failover measure should one email server crash or as a security verification means for email services.
How is this achieved?
Who will provide the email inboxes
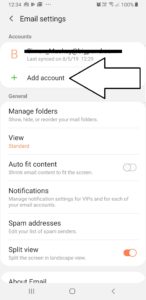
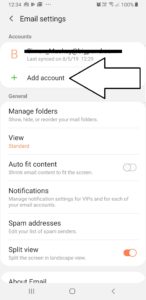
Add Account option in email settings on Android (Samsung) email app
Your workplace will give you an email address that is tied to your tenure with that employer. The provision of a tied email address will also apply for most college students or staff who have access to college IT resources. If you run a small business or other organisation with a Web presence and own domain name, your Webhost or domain name provider will offer at least one email inbox under the main domain name you purchased.
Most ISPs or telcos will provide you with at least one email inbox as part of your Internet-service deal. It will be something that is very common with fixed-line Internet service especially from major providers.
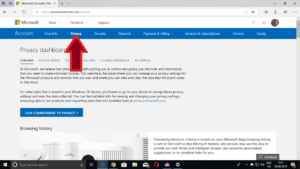
Of course, there are the Webmail providers like Outlook.com and Gmail who will provide you at least one email address for free. It also includes the secure email hosts who provide a secure user experience at a premium price.
Now we are seeing the rise of dedicated service providers who provide email inboxes as their main business. Such providers will offer Web-based or standard client-based access to these mailboxes.
What to look for

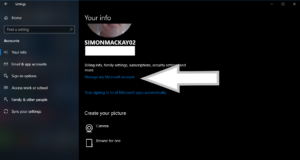
Account types offered by the Samsung Android email app
A feature I consider very important for email accounts is that they support multiple-device access and full “on-the-road” use. Typically it would mean use of a major Webmail host or a host that implements “hosted Exchange” or IMAP4 email protocols. This is important where we use a mobile device or secondary laptop computer to work our emails and want to work our email from anywhere.
You may find that a Webmail interface that allows the operation of multiple accounts from competing services may come in handy if you are using shared computers or public computing facilities.
How do you handle the multiple email inboxes
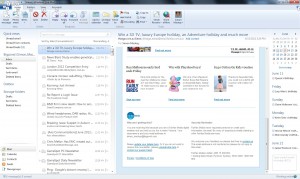
Different users may manage their email from multiple accounts using one of two paths. One is to use a single interface for all of the email accounts, with the other being to use different interfaces for different accounts.
It may include having all your personal email accounts operated with one interface like a Webmail interface while your work or business email accounts are operated with another interface like a business-optimised email client.
One email interface for all accounts
Most email interfaces, whether Web-based or client-based, will support the operation of multiple email accounts. In this case, using the one interface will underscore the idea of going to one email interface for all of your email activity.
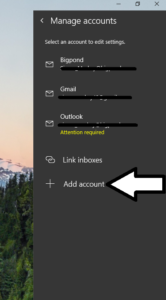
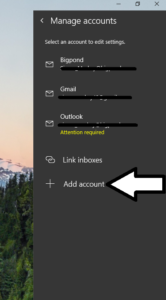
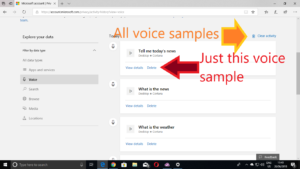
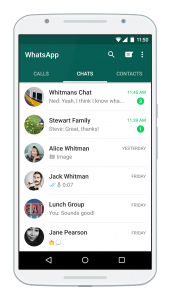
Your email interface will have an option in its account-management settings to add or delete email accounts. Most of the current interfaces will have a “quick-setup” routine for the popular Webmail providers; and will have a setup option for accounts using Microsoft Exchange, POP3 or IMAP4 accounts.
Receiving email
The user experience for reading your email will have separate inboxes for each of the accounts you manage. You may also find that some of the email interfaces like the GMail Web interface may offer a combined-inbox view for all of your email accounts with better interfaces using visual clues to differentiate each account.
Sending email
Should you send an email, you will be asked to choose which account you use to send your email via.
On some email interfaces where you choose the account you are operating at the moment like Windows 10’s Mail app, the account you are operating would be the one you send your email via. Other interfaces may require you to determine which account you send the email from when you click the “Send” button. As well, most of these interfaces may offer a default-account setting for new email, with the option to override this when you compose your new message.
The default behaviour for replying and forwarding would be to use the email service you received the email via for sending the replies or forwarding the email.
Your contacts list
Of course the contact list kept in your email interface will, in most cases, be shared amongst all of the accounts you operate.
Different email interfaces for different accounts
On the other hand, some of us may choose to operate each inbox with its own interface setup. This may be due to an email client not handling multiple inboxes how we want it or simply to delineate the operation of each inbox as a separate task.
This is a simple task with operating each interface with its own account. You will have to copy across contact details you want to use across multiple accounts if you operate them with separate interfaces.
A combination of this situation and the former situation will apply if you choose to operate some accounts with one interface and others with another interface. This is a useful practice for those of us who want that “church and state” separation between business and personal or public and private email activity.
Conclusion
Operating multiple email accounts may come in to play as a measure to protect your privacy and manage our email inbox properly.


 People who have a public-facing business life such as politicians or celebrities will maintain a public-facing email address to maintain an email correspondence consistent with that public-facing role. This is becoming more important where people in the public eye are becoming more vulnerable to “dirt-digging” – the practice of trawling for any information to discredit one’s reputation.
People who have a public-facing business life such as politicians or celebrities will maintain a public-facing email address to maintain an email correspondence consistent with that public-facing role. This is becoming more important where people in the public eye are becoming more vulnerable to “dirt-digging” – the practice of trawling for any information to discredit one’s reputation.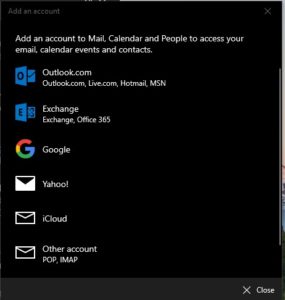




![Map of Europe By User:mjchael by using preliminary work of maix¿? [CC-BY-SA-2.5 (http://creativecommons.org/licenses/by-sa/2.5)], via Wikimedia Commons](https://homenetworking01.info/wp-content/uploads/2014/06/512px-Blank_map_europe_coloured.svg_-300x229.png)