Connected versions of classic novelties and giftware will be subject to severe scrutiny
An issue that is rearing its ugly head is the rise in availability of connected novelties and toys. They are toys, novelties, giftware, seasonal decorations and other items that are able to connect with your computer or network. This connectivity function is often sold as one of the key marketing features with it able to work with an online service of some sort.
When I talk of toys, I don’t just talk of what children play with with but also other toys that adults end up playing with. These can include the so-called “executive toys” that live on the office desk for one to keep the other hand busy while they are on the phone.
Who typically sells these products
Toys and novelties are typically sold through a large range of online and bricks-and-mortar retailers, whether they be toy stores, gift stores, souvenir outlets or multi-facet outlets including department and discount stores. In some cases such as rural areas, a store like a newsagent’s could even sell novelties or toys.
Another factor is that novelties are given away to people and businesses as a gift or premium. This can typically happen as part of a “loot bag” offered out at conferences or tradeshows or simply used as a giveaway during a presentation to encourage audience participation.

Seasonal decorations that connect to the Internet can also be a security or setup risk
The common factor here is that most of the outlets that sell this kind of product are staffed by people who don’t have much technological know-how. This can affect the procurement process affecting whether the item exhibited at the gift fair should be stocked, or providing customer advice during and after the sale including how to get the connected novelty fully operational.
Artisans who make these gifts and novelties

Your Amazon Echo will soon be expected to work with a wide range of toys and novelties
There is also the fact that craftspeople like to make various toys, novelties, gifts and other items and sell them directly to customers or on a wholesale basis. But they do want to add some extra functionality like musicality or flashing lights to some of their product lines.
Typically, if they want this extra functionality in these gifts that they make, they have someone else make and supply the necessary components like clockwork movements or electronic-circuit kits to fulfil the extra functionality in a pre-assembled form. Then the artisan installs the pre-assembled mechanisms or circuits in the toy or gift as part of putting the whole thing together.
It allowed these artisans to focus on their craftwork and build the items they want to sell, while being able to offer a wide range of goods. The same comments that apply to finished goods also apply to the various components and kits that are being sold to these artisans for their projects.
In this case, the artisans have to be aware of what they procure when they are being sold a “connected functionality” kit for installation in their projects. For them, they have to be aware of customer-support issues including setup and data-security issues regarding this extra functionality.
Connected modules for construction sets and similar hobbies
The same concept also extends to construction-set platforms like Meccano, Lego and FischerTechnik where children and adults build items using the pieces that are part of the respective platforms. In this case, anyone to do with these platforms could offer connected modules or kits that have the ability to control one or more items in their platform-based project like a motor, light or solenoid using an “Internet Of Things” approach. Here, these modules have to be able to seen as equivalent to a connected toy or novelty, especially if the idea is to implement cameras, microphones or GPS sensors.
It also applies to model railways, track-based car-racing sets and the like where they can be extended with functionality modules sold by the set’s vendor or a third party catering to these hobbies. Again the modules also need to be designed for security if they are capable of being part of the Internet of Things.
Use of these items
There is the desire for people to buy these toys and novelties as gifts for others in their life. It also includes the fact that the recipient wants to get the item “up and running” as soon as possible.
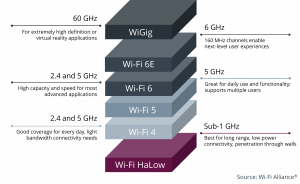
This will involve having the device connected to a host device through Bluetooth or USB or to a home network for proper reliable use. It should be about a standard process that is implemented for onboarding including the installation of any extra software.
Key security issues
A key security issue concerning the connected toy, novelty or similar device is that it can be an espionage item presented in an innocuous form. It can concern us both at home and in the office because we can easily be talking about items that are confidential and sensitive in our personal and business lives.
This was highlighted in a crime-fiction form to the Germanic viewership in Europe through the Munich-based Tatort “Wir Kriegen Euch Alle” (We Get You All) episode shown there on Sunday 9 December 2018. This story was focused around a connected doll that was given by strangers to various childrens’ families in middle-class Munich and was used as a surveillance tool to facilitate crimes against the families.
It underscored that Germany has some very strict policies where the sale of surveillance devices that are disguised as innocuous items isn’t allowed in that country. But, in the story, these dolls were imported in to Munich from a location in Austria which is a short drive away and facilitated by the Schengen Agreement in the European Union.
Let’s not forget the recent cyberattacks such as the Mirai botnet that were facilitated by dedicated-purpose devices like network-infrastructure equipment and videosurveillance cameras which were running compromised software. Then there are factors regarding data-storage devices and “bag-stuffer” novelties given away during business conferences where there is the possibility of them being loaded with questionable software.
What would I like to see
Security
There has to be identification on the toy’s or novelty’s packaging about what kind of sensors like location sensors, microphones or cameras that the device has, as well as whether the device transmits data to online services. This includes whether the device does this directly or via intermediary software running on other computer devices such as mobile devices running companion mobile-platform apps. Even a hang tag attached ti the novelty could highlight what kind of sensors or online services it uses which would be important for those items sold without packaging.
Preferably, this can be achieved through standard graphical symbols indicating the presence of particular sensors or the use of online services and social networks. It can also identify whether the toy’s or novelty’s functionality are dependent on these sensors or online services.
App stores and other software platforms that host “connector” software have to implement stringent permissions for these kind of devices especially if they use a microphone, camera or location sensor. There could be standards on whether the software is allowed to record from these sensors over a long time or keep the recording persistent on the host device or online service.
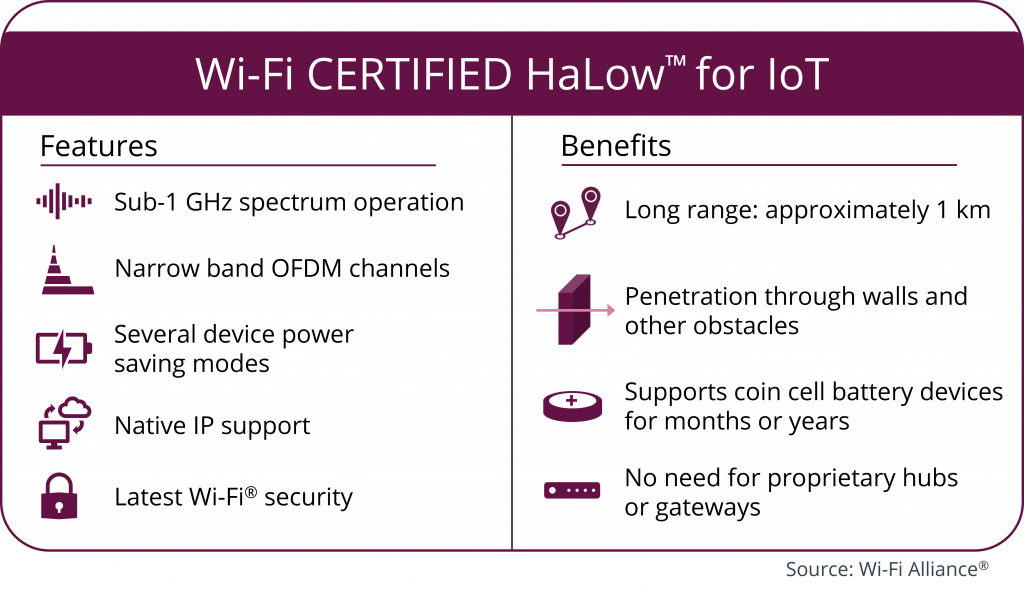
A limitation I would also like to see for connected toys and novelties that if they work with another computing device including a smart speaker, the connection can only be effectively within the same premises. This can be tested through the use of a peripheral-grade connection like Bluetooth or USB to a computing device or limiting the range of discovery for network-based devices to that of the same logical private network or subnet. Here, it represents all the devices on the LAN side of a home-network’s router and excludes devices existing on other logical networks served by the same physical device like “guest” or “community” networks.
As far as Bluetooth is concerned, the toys should implement authentication processes during the setup phases. Then the device ceases to be able to be discovered once it is paired with a host device. It is like what we are seeing with Bluetooth headsets and similar devices that have been recently released. They may also have to work on a limited radio range to prevent successful connection from a distance.
There should also be a simple “factory-reset” process to allow the user to place the toy or novelty in to setup mode, effectively wiping data from the device. This allows a recipient to effectively “claim possession” of the device as if it is new, avoiding the situation where they may be given something that is compromised to do what someone else wants it to do. It also applies to situations where you are dealing with ex-demo stock or gift-fair samples.
This should also apply to online services associated with these toys or novelties where the user has proper account control for the device’s presence on that service and any data collected by that device.
There are devices that observe particular functions according to a particular device class supported by many platforms like a novelty nightlight or illuminated Nativity scene that works with a “smart-home” setup or a novelty Bluetooth speaker. These devices have to work according to the standards in force for that device class and its connection to the host device or network. It is more important where the device may perform further tricks while running alongside dedicated vendor-created software but is able to have basic functionality without this software.
A software-level security approach could be achieved through an open-source or peer-reviewed baseline software that ticks the necessary boxes. This would apply to the firmware installed in the device and any apps or other companion software that is required to be run on other computing devices for the novelty to operate. It also includes a requirement that this software be reviewed regularly for any bugs or weaknesses that could be exploited, along with compliance requirements.
This could be assessed according to a set of European norms because the continental-European countries are very concerned regarding privacy thanks to their prior history.
As far as modules for integration in to toys, novelties and giftware is concerned, the modules should meet the same requirements as finished products that would have the same functionality. Craftspeople should also be aware of data security and user privacy issues when it comes to choosing modules for their projects that are dependent on computer devices or networks.
Setup and Connectivity
Another area that is a sore point for connected toys and novelties is bringing these devices on board for you to use. In a lot of cases, this is exacerbated through awkwardly-written instructions that can test one’s patience and not much knowledge about what is needed for the device to work fully.
The device packaging could use Wi-Fi, Bluetooth or other standard logos to indicate what kind of connectivity it needs to operate fully. This is to be highlighted with the “app store” logos for various operating-system app stores if the device is dependent on companion apps for full functionality. Similarly, use of other official platform logos can be used to identify compatibility with platforms like smart-TVs or voice-driven home-assistants.
Simple-yet-secure setup and onboarding procedures are to be paramount in the design of these devices. For Bluetooth-based devices, they should use “simple-pairing” such as pressing a button on the device to make them discoverable. This is even made easier with a trend towards “out-of-the-box” discoverability if the device isn’t paired with any host. Then the user activates their host device in “Bluetooth Scan” mode to discover the device, subsequently with them selecting the device through its presentation name.
Windows, Android and iOS are even implementing simplified device-discovery routines for Bluetooth devices, with the ability to lead users to visit the app store to install complementary software. This will make things easier for users to get the toy or novelty up and running.
Wi-Fi-based devices would have to use WPS-PBC push-button setup, Wi-Fi Easy Connect, or other simplified setup processes for integration with the home network. It also applies to other network connection standards where you have to enrol the device on to that network.
Smart-home devices that implement Zigbee, Z-Wave and similar standards also have to implement simplified discovery protocols implemented in these standards to bring them on-board.
In relationship to security, I underscored the need for use of device-class standards as much as possible. But it also applies to connectivity and useability where a device that honours device-class standards is also easier to use because you are operating it the same for its peers.
Conclusion
This year will become a time where security and useability will be of critical importance when toys, novelties and other similar goods that connect to the home network and the Internet are designed and sold to consumers. Here, these issues may avoid these kind of toys ending up in disuse due to security or setup issues.