Another year of HomeNetworking01.info
Technology
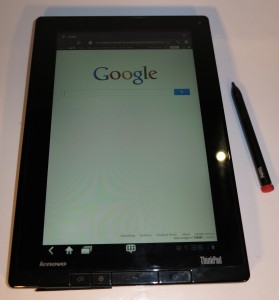
Mobile Computing platforms
The Android mobile computing platform has, over the past year, become an increasingly-credible platform that overtakes the Apple iOS mobile computing platform. This has been exemplified through the Samsung Galaxy S3 smartphone, the Samsung Galaxy Note phone-tablet bridge device and the Google Nexus 7 tablet. This has even had apple take Samsung to court concerning “trade dress” and similar patents that Samsung copied in their earlier Galaxy S and SII products.
Regular computing platforms
Another set of major technology changes over the past year had come about in the form of new versions of the Windows and MacOS X regular-computer operating systems. These versions, known as Windows 8 and MacOS X Mountain Lion respectively, have introduced various mobile-computing concepts such as touch-driven operation and the app store to the regular computer.

The long-lasting battery can allow the Fujitsu to work well for a long day of hotspot surfing at inner-city cafes and bars
As for the hardware, Intel had launched the third-generation “Ivy Bridge” classic-instruction-set processors with improved integrated graphics. This has raised the stakes for regular-computer graphics especially in the portable-use arena.
Bluetooth Smart Ready
The Bluetooth standard now embraces the 4.0 “low-power” variant which supports sensor and control devices that can work on 2 AA batteries or a watch battery for something like six months. This requires that the sensor devices work with a host device that implements Bluetooth 4.0; and this feature is slowly creeping in to all of the credible smartphones and tablets as well as some regular computers like Apple’s latest MacBook lineup and some of the Windows-based computers.
Awareness of malware targeted at the Macintosh platform
It is also the era that the Apple Macintosh platform is gain a similar user base to the Windows platform as far as regular computing is concerned. It doesn’t matter whether the core task for that computer is to be office work or creative work like media editing or playback, with some Windows computers being used for the latter purpose.
This has drawn malware creators to the idea of using the Macintosh platform as an attack vector, mainly through the use of cross-platform runtime environments like Java or Adobe Flash. This is due to the ability to quickly write and deploy the same version of software to run on both Windows and MacOS, with the runtime module liaising with the file system and other operating-system services/ Lately this vector has been taken further with zero-day attacks because the Java runtime isn’t updated as quickly and as regularly as the native-code software for the main regular-computing platforms.
We are being encouraged not to implement these runtime platforms unless necessary and I have raised the idea of compiling Java-written code to platform-native logic when writing for a regular-computing platform rather than creating intermediate code that requires the runtime component. This is so one doesn’t have to run a Java runtime component which can be used as an attack vector or allow a slow operating environment. Similarly, there will be a requirement by Symantec and others to write “security runtimes” that check for malware in Adobe Flash or Java intermediate code.
Network technology
802.11ac wireless networking
As for the small network, there have been a few trends concerning it. For example, a pre-release version of 802.11ac Gigabit wireless networking has been released but this is intended to work on the 5GHz radio spectrum.
Wi-Fi Direct wireless-network setup
Similarly, we have become more aware of the Wi-Fi Direct wireless-network setup concept. This is more about creating a Wi-Fi “personal-area network” either as an alternative to Bluetooth for wirelessly connecting peripherals to a host computer or setting up a temporary “on-the-road” network for mobile devices, laptops and network-connected peripheral devices.
I had reviewed a device which was an example of this concept in the form of the Kingston Wi-Drive, one of the “wireless portable storage servers” that are being promoted for use with smartphones and tablets. Another class of device that is exemplifying this concept is some of the recent crop of network speaker systems that can play music from a computer device via a Wi-Fi network that it is part of or can create itself. They use either Apple AirPlay or the open-frame DLNA standards to transfer the audio content from the computing device to the speakers.
HomePlug AV 500
Another trend for “no-new-wires” networking is the use of HomePlug AV 500 which is a high-throughput variant of the HomePlug AV powerline network. This will have the same situations as the HomePlug 1.0 Turbo network where all the endpoint devices that exist on that segment have to he the high-speed variant for the segment to work at the high bandwidth.
WPS in a multi-access-point wireless network
A question I have answered myself in the course of troubleshooting and optimising a home network was how the WPS easy-setup solution would cope with a multi-access-point wireless network. These kind of network setups are often required where there are building setups that could impede radio-wave transmission, such as interior walls made of double-brick, stone, reinforced concrete or the existence of metal walls.
The above-mentioned networks would have two or more access points which are linked to each other via an Ethernet or HomePlug AV wired backbone. All the access points operating on the same band are set to the same SSID and security parameters but are set to different radio channels so that the wireless client devices can roam between the access points seamlessly.
Here, I found that as long as the access points that have this feature are set up to persist their current setting when you engage the WPS push-button setup function, this function won’t affect the proper operation of this extended service set. What’s more, you can use this quick-setup routine at the access point closest to where you are intending to use the new device you are setting up.
Milestones
Two milestones have happened over the past year. One was the death of Steve Jobs who. along with Steve Wozniak, founded Apple in the mid 1970s. This led to the arrival of one of the first credible personal computers in the form of the Apple II, the commercialisation of the graphic user interface with the Macintosh and eventually a credible mobile computing platform with the iPhone and iPad. When I heard that Steve Jobs was falling ill with the cancer, I saw it in a similar light to Bill Gates leaving Microsoft – the foundation stones of personal computing coming away.
Another milestone that was celebrated this year during the Opening Ceremony of the 2012 London Olympics was Sir Tim Berners-Lee. Her was the founder of the World Wide Web and, effectively, the Internet as we know it today.
This site
I have increased the quantity of Ultrabooks and similar computers reviewed on this site, focusing on them being secondary travel computers rather than main or sole computers. I have also revised the laptop buyers’ guide to encompass this class of computer.
Similarly I am increasing the amount of coverage dedicated to the online lifestyle. With this, I have given special coverage to the sports scoreboard apps that you can download to your smartphone or tablet so these devices can become sports scoreboards. I have tied it in with some of the main sporting events.
As well, part of giving some more time to travel and lifestyle is to establish a “travel and lifestyle” page which will have useful information for travellers and for people who integrate their IT in to their lifestyle.
My post on the Australian Audio & AV Show 2011 has allowed me to sum up the trend towards network-driven audio and video, especially as it is being considered of respect at the top end of the market. This has intensified my interest in the DLNA-compliant home media network because of it being respected by hi-fi manufacturers of respect.
I have spent some time writing some advisory articles on common computer-usage topics. One of these was a two-part “Email Essentials” series (1, 2) where I explained about basic email-usage concepts, something I have often had to help people who aren’t competent with computers on. I augmented this with another article about using email for sending messages to be “taken further”, which was targeted at people who regularly use Facebook, Skype, iMessage, SMS and other messaging systems.
These two articles are based on work that I have done whenever people ask me for assistance with their computers. I have also written up an article about dealing with that “hair-trigger” mouse which can happen with different mice and as they get used more.
As well, I have written an article on how to keep your computing skills alive and relevant when you retire from active work life. This encompasses what computer system to use as your main computer setup, including the idea of buying out your laptop or desktop that you have used at your work; as well as keeping the skills alive.
Because I have reviewed some business-grade laptop computers and other computer targeted at the business user, I have written an article about this class of equipment becoming relevant to the small-business and SOHO user. Typically, the distributors tend to pitch this class of equipment at the “big end of town” i.e. the larger corporations who have a large fleet of these computers, and these products are not made easily available to the smaller operator even though they can do the job as well for them.
I had written up an article about setting up for Internet when you move to a location in France. This is due to the highly-competitive Internet and triple-play market that exists in that country and I have encompassed some coverage about the Freebox Révolution Internet gateway and set-top box as being an example of what is being offered as carrier-provided equipment in France.
I have given a fair bit of coverage to the cloud-computing trend especially as this is frequently referenced in the computing press and bandied about by people selling IT solutions to small business. This was instigated by an interview that I did with — regarding secure computing in the cloud-computing age and had written an article about what small business needs to look for when they sign on to this kind of service.
I have given some coverage to the issue of device firmware updates and field-delivered software to computing devices. This is in response to legal action that was taking place in the US concerning the device firmware updates that were being applied to HP printers. This legal action was raising the possibility of loading modified firmware in to a device that could facilitate espionage or other undesirable activities. Here, I was describing the trends that occurred with the firmware-update practice over the years and raised security and updating issues concerning this practice, and the fact that the firmware-update ecosystem must deliver a secure update for the device and when we deliver the first update for a device, we deliver one that brings it to expected functionality once and for all.
Conclusion
Expect a very interesting next year for regular and mobile computing life as Windows 8 and MacOS X Mountain Lion merge the context of mobile and regular computing with different devices suiting different needs occupying particular spaces in the home and small business network.