A wireless router set up in the ordinary way as a base station or hub for your home network isn’t at risk of the KRACK exploit
The computing press has been awash with articles regarding a recently-discovered security vulnerability that affects Wi-Fi wireless networks. This vulnerability, known as KRACK, compromises the authentication process associated with the WPA2 security protocols that most Wi-Fi home and business networks implement.
What is affected
But it mainly affects client devices like laptops, smartphones and the Internet of Things which connect to Wi-Fi networks using WPA2 facilitated through software that isn’t patched against this risk.
It also can affect Wi-Fi infrastructure devices that serve as a repeater or client-side bridge in a Wi-Fi wireless network segment – this encompasses Wi-Fi client bridges used to connect desktop computers or smart TVs equipped with Ethernet connectivity to a Wi-Fi network, Wi-Fi repeaters, distributed-Wi-Fi setups and mobile devices implementing “bridge-to-Wi-Fi” functionality.
Data security risks
The security and privacy risk occurs at the media level of your network connection which would represent the Wi-Fi wireless link to the access point / router.
If you use higher-level encryption protocols like gaining access to Internet resources through SSL / TLS encryption which includes “https” Webpages, implementing a client-based VPN or using IP telecommunications apps that implement end-to-end encryption, you have reduced the risk factor for your data security that the KRACK vulnerability poses. Access to LAN-based resources like your NAS or printer from within your network can be a risk with Wi-Fi clients that aren’t patched to mitigate this risk as with unencrypted Internet resources.
Current remediation efforts
This situation has been rectified for regular computers running Windows 7 onwards through a patch that Microsoft rolled out as part of the October 10 security update. Here Microsoft didn’t disclose this vulnerability until there was a chance for all of industry to have patches in beta testing or “ready to roll”.
Just lately (1 November 2017 AEDT) Apple released patches for MacOS High Sierra, Sierra and El Capitan versions; and iOS 11.1 (iPhone 7 onwards, iPad Pro 9.7″ (2016) onwards); tvOS 11.1 (4K Apple TV onwards) and watchOS 11.1 to address this issue. The Intego Mac Security Blog post that I culled these details from was miffed about the fact that the large number of iPhone 6 and earlier devices that are still in operation have not been addressed. I would also extend this concern to the older iPad and iPod Touch devices that are also in operation such as those iPod Touches the kids use or the iPad in your living room.
On December 2 2017 US PT, Apple released the iOS 11.2 update which provided this protection for iPhone 5S, iPhone SE and all model variants of the iPhone 6. This update also applies to the 12.9″ iPad Pro (1st generation), the iPad (6th generation), the iPad Air, the iPad Mini 2 onwards; and the iPod Touch (6th generation).
Other regular-computer and mobile operating systems are being updated with security patches that are coming online through the next two months or are already online.
There will also be various pieces of client-side security software that will be updated with extra code that provides extra defence against the KRACK Wi-Fi vulnerability for both the software and the host computer.
The devices you will find as having a strong risk factor for your network are “dedicated-purpose” network devices like Internet AV devices, “smart-home” devices, videosurveillance cameras and the like that don’t benefit from regular firmware updates. This will mainly affect those devices that manufacturers are declaring “end-of-support” on or a lot of “white-box” devices sold by multiple vendors. But check your devices’ manufacturers’ Websites for new firmware that will patch the device against this vulnerability.
This will not affect the typical home or other small network that is based around a wireless router. Nor will it affect networks that implement multiple Wi-Fi access points connected to a wired (Ethernet or HomePlug) backbone. This is because you are dealing with devices that serve as a Wi-Fi base station for that particular wireless network segment.
But if you have Wi-Fi infrastructure devices using some sort of repeater or bridge functionality, check with the vendor for a firmware update for your device.
As well wireless router and access-point manufacturers, especially those courting the business and allied markets, will offer newer firmware to harden their devices against the KRACK vulnerability.
Remember that well-designed devices will implement at best an automatic software-update process or you may have to visit your device’s Settings, Setup or Configuration menu to download new firmware.
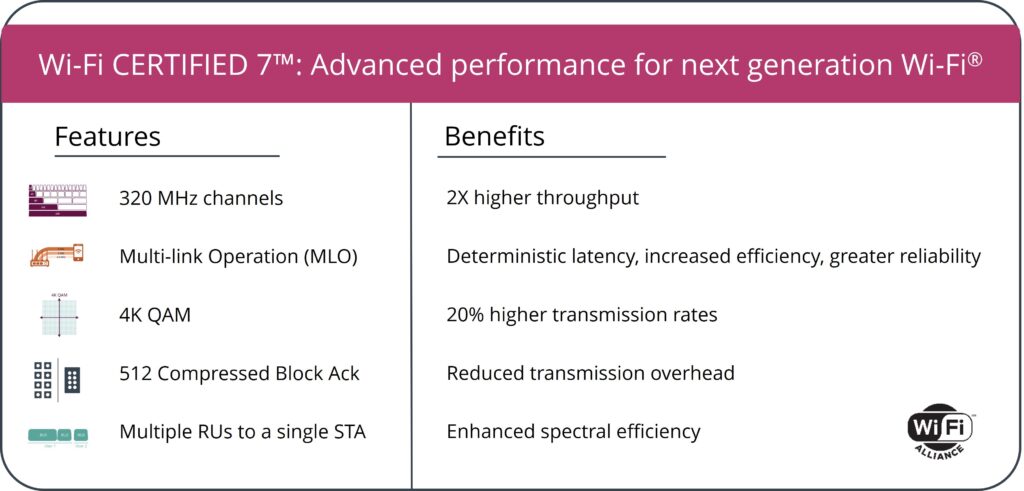
As well, the Wi-Fi Alliance have updated their certification tests for network hardware to be sure that such hardware isn’t vulnerable to this risk. These certification tests will be required before a product can show the Wi-Fi Certified logos and will affect products being introduced from this month onwards.
Keeping your network secure until new software is available
If you run Wi-Fi network infrastructure hardware that implements repeater or bridge functionality, disable the Wi-Fi client mode or repeater mode on these devices until your device is running firmware hardened against this vulnerability.

The HomePlug powerline adaptor can help with mitigating risks associated with the KRACK WPA2 Wi-Fi network vulnerability
You may also have to set up your home network with multiple access points linked to a wired backbone as the preferred way to extend the network’s coverage or reach to another building as has been done with this man-cave. A good example of this is to use a HomePlug wireless access point kit which uses your home’s AC wiring for this purpose. If you use a “Mi-Fi” mobile router that supports Wi-Fi data offload, disable this functionality until it is loaded with the latest secure firmware.
Similarly, use a wired network connection such as Ethernet or HomePlug to connect sessile devices like desktop computers, Smart TVs, printers and the like to your home network. This may not be feasible with those devices that only support Wi-Fi connectivity as their network-connection option.
Conclusion
You can mitigate the risk of the KRACK WPA2 Wi-Fi network vulnerability as long as you keep your computer equipment running software that is patched with the latest security updates.
If you use Wi-Fi infrastructure devices that work as a Wi-Fi client like repeaters or client bridges, these have to be updated with the latest firmware from their vendor. As well, use of wired backbones and access points for expanding your home network’s coverage will achieve the proper level of security against this risk if you are dealing with client-capable Wi-Fi infrastructure devices that aren’t updated with the latest software.
Let’s not forget that higher-level encryption protocols like SSL or client-side VPNs do mitigate the risk of data theft through this vulnerability.
Updated (1 November 2017 AEDT) to reflect the latest concerning what is happening with the Apple platforms.
Updated (11 December 2017 AEDT) to reflect the increased number of iPhones and iPads protected against the KRACK exploit by the iOS 11.2 update