Article
Legislation or regulation to come about to open up the app-store market on mobile devices to competing providers
How the Open App Markets Act wants to remake app stores – The Verge
What the Open App Markets Act means for future of Big Tech (fastcompany.com)
From the horse’s mouth
US Congress
Open App Markets Act (Follow this law through Congress)
My Comments
At the moment, if you want to add functionality to your smartphone or tablet, you have to use the Apple App Store or the Google Play Store to download the necessary apps. Some Android phone manufacturers like Samsung and Amazon run their own app stores with the former operating theirs alongside Google’s app store and the latter in lieu of that app store.
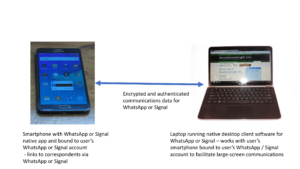
This process also affects post-download transactions like purchasing the software after a trial, subscribing to the services associated with the software or buying microcurrency for a game using real money. With services like Netflix or Spotify or mobile ports of some desktop software, you use the service’s desktop user interface to sign up and pay for subscriptions then you log in to the user account you created for that service using the mobile app to benefit from what you paid for.
The same approach is being used for the ChromeOS platform and Microsoft and Apple want to push this on to their Windows and MacOS desktop computing platforms. This is more so with Microsoft and the ARM-powered Windows laptops or offering lightweight “S” variants of Windows for cheaper computers. It is also implemented with games consoles, connected-TV/set-top-box platforms, printers, network-attached storage devices, routers, connected vehicles and the smart home as a way to add functionality to these platforms.
This may even apply to app stores on regular computers like the Windows Store
Here, some of the companies in Big Tech want to provide that same kind of walled garden that is expected with games consoles for other computing devices as a way of providing some perceived “simplicity” and security for these devices.
Concern has been raised about this approach due to frustrating competition for apps on these platforms. It includes a monopsony approach where software developers are disadvantaged due to the app store charging commissions on software-related transactions or exacting onerous terms and conditions on software developers who want to have their apps available on the popular mobile platforms.
This is an issue that has been brought about by the Fortnite saga where Apple frustrated Epic’s wishes to sell microtransactions, subscriptions or similar services for Fortnite independently of Apple even for iOS ports of that game. There is similar activity going on in the European Union with the Digital Markets Act to push for competition in the mobile-computing-device realm while the authorities in charge of market competition in the UK and Australia are examining this issue.
What is the Open App Markets Act about?
What the Open App Markets Act means is that competing app markets can exist on mobile and similar-use platforms like iOS and Android. It also requires that these platforms have a requirement to allow users to sideload apps to their devices and the platform can’t default to its own app stores.
Sideloading is primarily transferring software from a regular computer or external / network file storage to the mobile or other device in order for it to run on that device. This is similar to the way we have installed software on our Windows, Macintosh or Linux computers for a long time. Here, we have inserted a floppy disk or CD-ROM in to a computer and ran an installation from that storage medium to have the software on the computer. Or we downloaded the software from the developer’s Website or a download site to our computer’s hard disk and ran the installation program associated with that software to install it.
It could also extend to software developers making the software available to download or purchase from their own Web presences, including processing any post-download payment transactions there. This means that the software developer gains effective control over their software through its lifecycle.
If software developers wish to implement post-download transactions for their software such as converting a trial version to a full-service program, offering subscriptions or selling microcurrency for a game, they can use a competing storefront or facilitate their transactions on their own Websites.
Who would it primarily benefit?
A user group that would benefit from the competitive app market would be gaming enthusiasts. Here, they would benefit from games-focused app stores like Steam, Epic and GOG who run their own leaderboards, online game saving, and online forums. Similarly, games developers would be running their own app stores for their games titles, continuing to offer the same kind of integrated functionality.
I also see Microsoft behind this idea because of software development being their founding stone with an example being the XBox One designed from scratch to support home-developed games. This is because they want to run app stores as a way to make it easier for up-and-coming software developers to put their wares on their market.
What are the issues here?
One key issue that would come up in my mind is a replication of the “bulletin board” or “download site” era that existed before and during the early days of the Internet. This is akin to the “shovelware” magazine-cover CD-ROM era that existed in the early days of optical data storage. That is where you had online or offline collections of poor-quality software available for download or installation on your regular computer. It is something that has affected some app stores in their early days where they were replete with poor-quality apps.
Here, there was very little effort regarding quality control when it came to making software available on a bulletin board or download site or adding software to an optical disc that was attached to a computer magazine. This is compared to most app stores where the people who run the stores vet the software before it is published as well as running “editor’s choice” or “spotlight” programs to feature good-quality software,
Apple and Google challenge the competitive app store approach because they see exclusive app stores as a way to maintain standards regarding software for their platforms.
Here, they see this primarily with data security and user privacy. But they also see this with maintaining legal and social expectations regarding the kind of software available on personal devices. This ranges from issues like suitability for children and suitability to use in the workplace or around your family; along with being able to facilitate access to undesireable content like hate speech or disinformation.
How could these issues be answered?
Computing-platform, operating-system and device vendors, amongst other strong voices in the personal/business IT and cybersecurity world could implement one or more “seal-of-approval” systems on apps or app stores. There would even be various legal protections and requirements placed on the software and app stores like intellectual-property or media-classification requirements, Here, the software or app stores have to maintain certain quality and similar standards before acquiring that “seal of approval”.
Endpoint-security logic that is part of the operating system or a third-party endpoint-security program offered by a brand of respect would add extra friction to installing or running software that doesn’t have one or more of these “seals of approval”. As well, such software would be required to identify and easily remove such software.
Similarly, these companies could vet software developers’ access to software-development kits and application-programming interfaces so that the developer has to be in “good standing” to use the features that matter in an operating system. As well, software-authentication regimes will be implemented in a strong manner for any software that is distributed or installed on these devices.
Is there a risk of a limited rollout of open app-market features
There can be a risk of Big Tech creating versions of their app-store-driven computing platforms for particular geopolitical areas when each area enacts open-app-market legislation.
In this situation, when a user registers a new device or the device’s operating system is updated, there would be logic to test whether the device is within a country or region under an open-app-market mandate then deliver a compliant version of the software to those areas. That is while a noncompliant version of the software is delivered to new or updated devices in areas that don’t have the open-app-market mandate.
This is similar to an issue faced in Australia with the motor industry where vehicle builders are “dumping” vehicles that are less fuel-efficient in to that market. That is because there aren’t the fleet-wide vehicle-efficiency mandates there that are similar to those mandates affecting USA, Europe or South East Asia.
Here, the issue that would be raised is having markets that aren’t regulated with open-app-market mandates being areas to continue the status quo regarding anticompetitive behaviour. Add to this intense lobbying of government or political parties by Big Tech to continue the same kind of behaviour with impunity.
Conclusion
What may be coming about for smartphones, mobile-platform tablets and similar devices is that governments will be forcing open the app-store markets for these devices so that users can seek software from competing suppliers.